
Blog
What is an ASN and How It Helps in Cybersecurity: A Practical Guide
Written By Usama Shabbir, WhoisFreaks Team Published: August 07, 2025, Last Updated: April 09, 2026

Blog
Written By Usama Shabbir, WhoisFreaks Team Published: August 07, 2025, Last Updated: April 09, 2026
An ASN, or Autonomous System Number, is a unique numeric identifier assigned to a group of IP networks managed under a single routing policy. Internet service providers, cloud platforms, universities, and large enterprises each receive an ASN. Border Gateway Protocol (BGP) uses these numbers to route data between networks across the entire internet.
Security teams use ASN WHOIS API to trace the origin of malicious traffic, apply network-level blocks, and detect BGP route hijacking before it causes outages. This guide covers what ASNs are, how they work, how they are assigned, and the specific cybersecurity scenarios where ASN intelligence gives analysts an actionable advantage.
An Autonomous System Number (ASN) is a unique identifier assigned to an autonomous system (AS), which is a group of one or more IP networks managed under a single, clearly defined routing policy. ASNs are assigned by the Internet Assigned Numbers Authority (IANA) through five Regional Internet Registries: ARIN (North America), RIPE NCC (Europe and the Middle East), APNIC (Asia-Pacific), LACNIC (Latin America), and AFRINIC (Africa).
ASNs come in two formats. The original 16-bit format allows for 65,536 values (0 to 65,535), with 64,512 to 65,534 reserved for private use. The 32-bit format, introduced in 2007, extends the range to over 4.29 billion values. As of 2025, roughly 120,000 ASNs are actively allocated globally.
In cybersecurity, ASNs identify the network origin of internet traffic. Security analysts use ASN data to attribute attacks to specific network operators, block traffic from known-malicious autonomous systems, and detect unauthorized BGP prefix announcements.
Autonomous systems are classified into three operational types based on how they connect to other networks:
Connects to two or more other autonomous systems. This gives the network redundancy. If one connection fails, traffic reroutes through the other. A multihomed AS does not allow other networks to use it as a transit path.
Connects to only one other autonomous system. It sends and receives its own traffic but does not pass traffic between other networks. Most end-user organizations operate as stub ASes.
Connects to multiple ASes and allows traffic from one AS to pass through it on the way to another. Large ISPs and backbone providers operate transit ASes. These networks carry the majority of global internet traffic.
Understanding which type of AS is behind a suspicious IP or traffic source is directly relevant to threat attribution. A transit AS hosting malicious traffic can affect many downstream networks simultaneously.
The internet is made up of thousands of different networks. These networks need a way to talk to each other safely and correctly. That’s exactly what ASNs help with.
Here’s why we need ASNs:
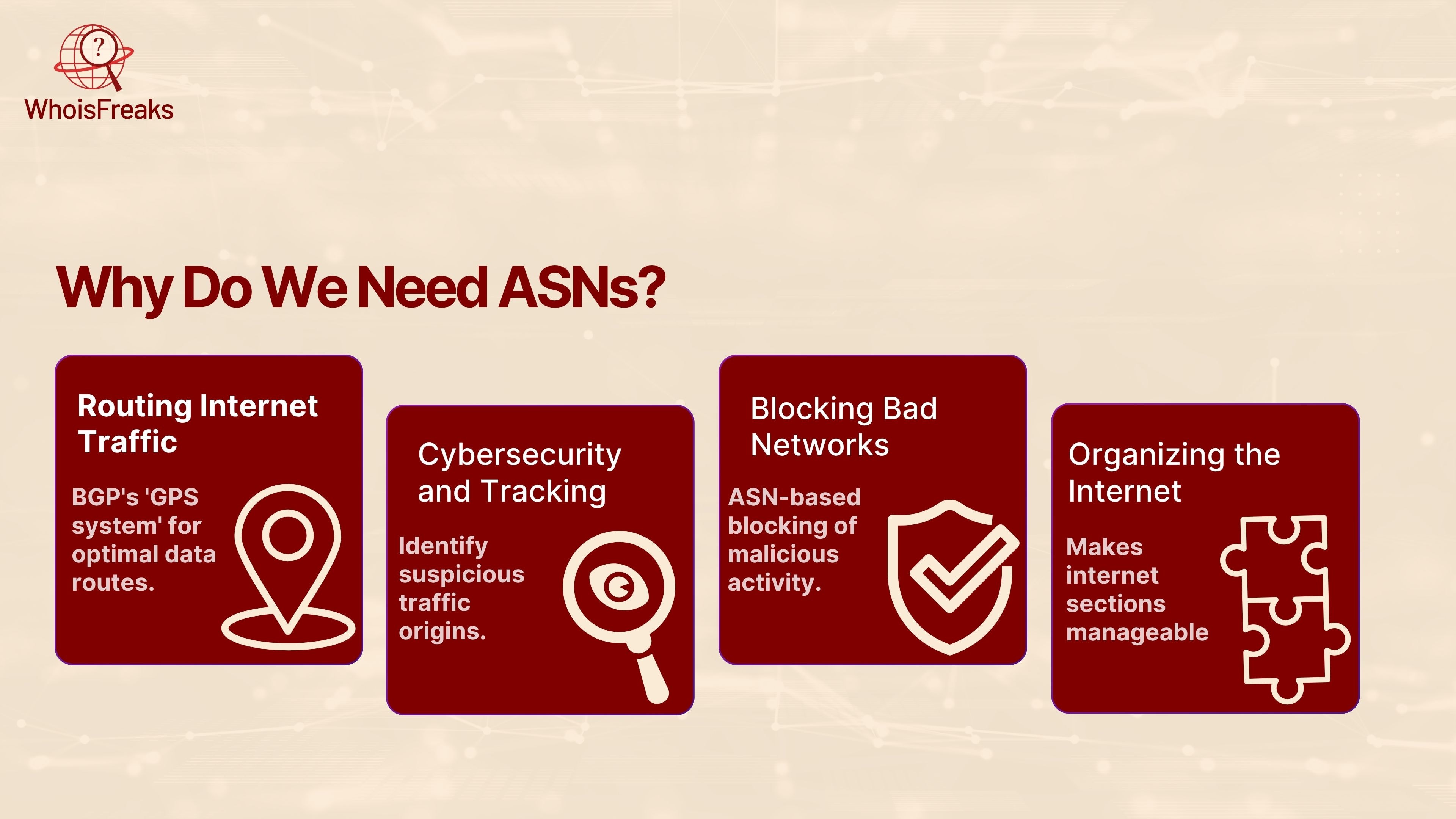
BGP (Border Gateway Protocol) involves the use of ASNs, which is a form of the GPS system of the internet. It aids in providing data through the optimal route amid networks.
Using ASNs, one can understand where network traffic was launched. It can be of great help in cybersecurity. Having suspicious traffic or dangerous traffic, with the knowledge of the ASN number, we can establish the source of traffic.
If a certain ASN is known for hosting malicious activity (like phishing domains or attacks) security teams can block it. This is called ASN based blocking.
In absence of the ASNs, various kinds of networks within internet would be chaotic and difficult to control. Every ASN creates a section of the internet manageable and simple to administer.
In short, ASN security is about using these unique numbers to keep the internet running smoothly — and more importantly safely.
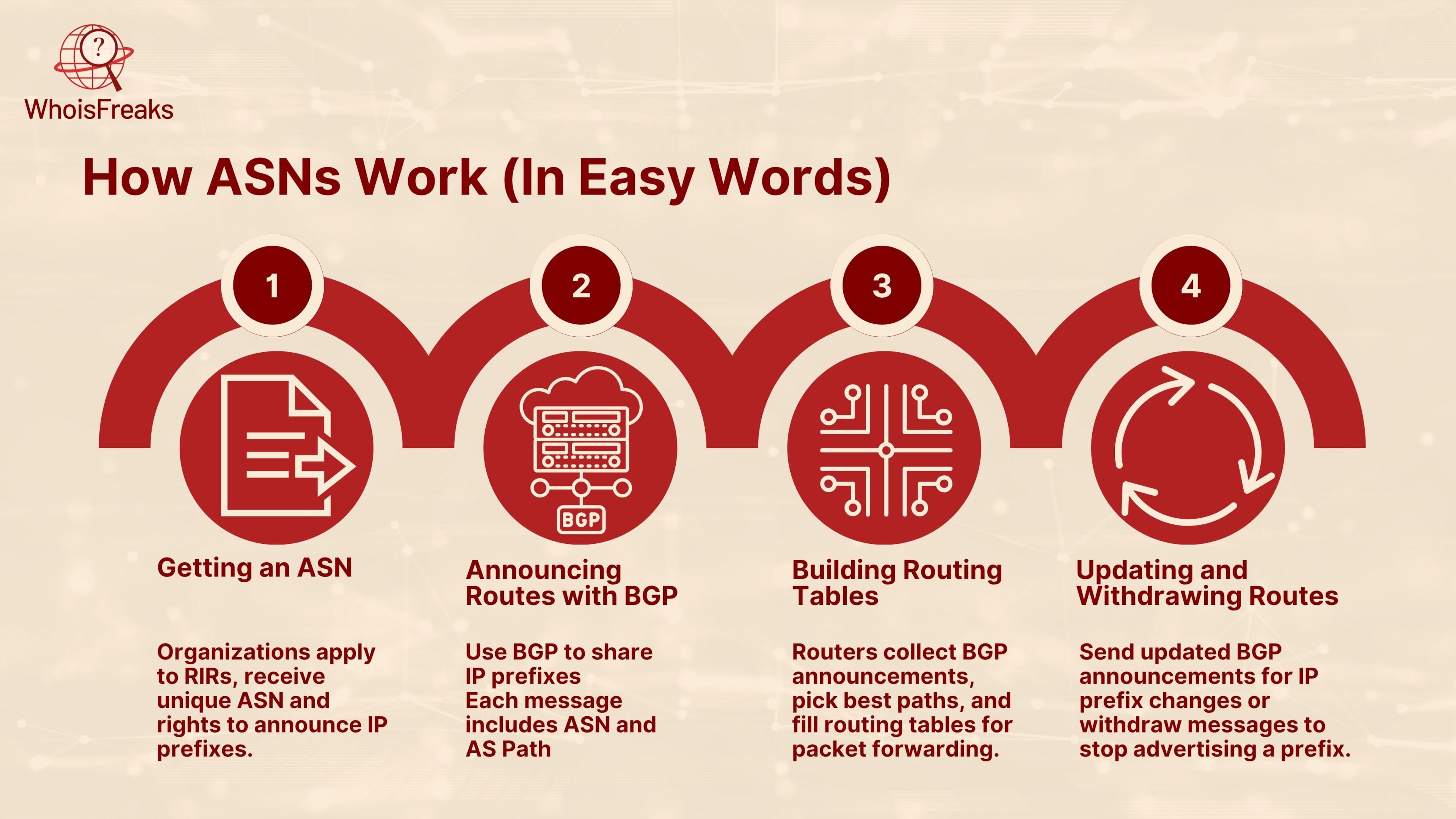
Each BGP message includes your ASN and the path it will take (the AS path). For example:
Prefix: 203.0.113.0/24AS Path: 64500 → 64510 → 12345
Security teams use ASN data across several distinct workflows. Understanding which autonomous system is behind a given IP address tells analysts who operates the network, where it is geographically registered, and whether it has a documented history of malicious activity.
When a SIEM alert fires on a suspicious IP, the next step after identifying the ASN is running a full IP Whois lookup to retrieve the registered network block and abuse contact directly. ASN ownership data turns a raw IP into an organizational context.
If an autonomous system is confirmed as a source of volumetric DDoS traffic, scraping, or coordinated phishing campaigns, security teams apply firewall rules that block the entire ASN's IP prefix range rather than blocking individual IPs. This is more durable than IP-level blocking because the attacker cannot simply rotate to a new IP within the same ASN.
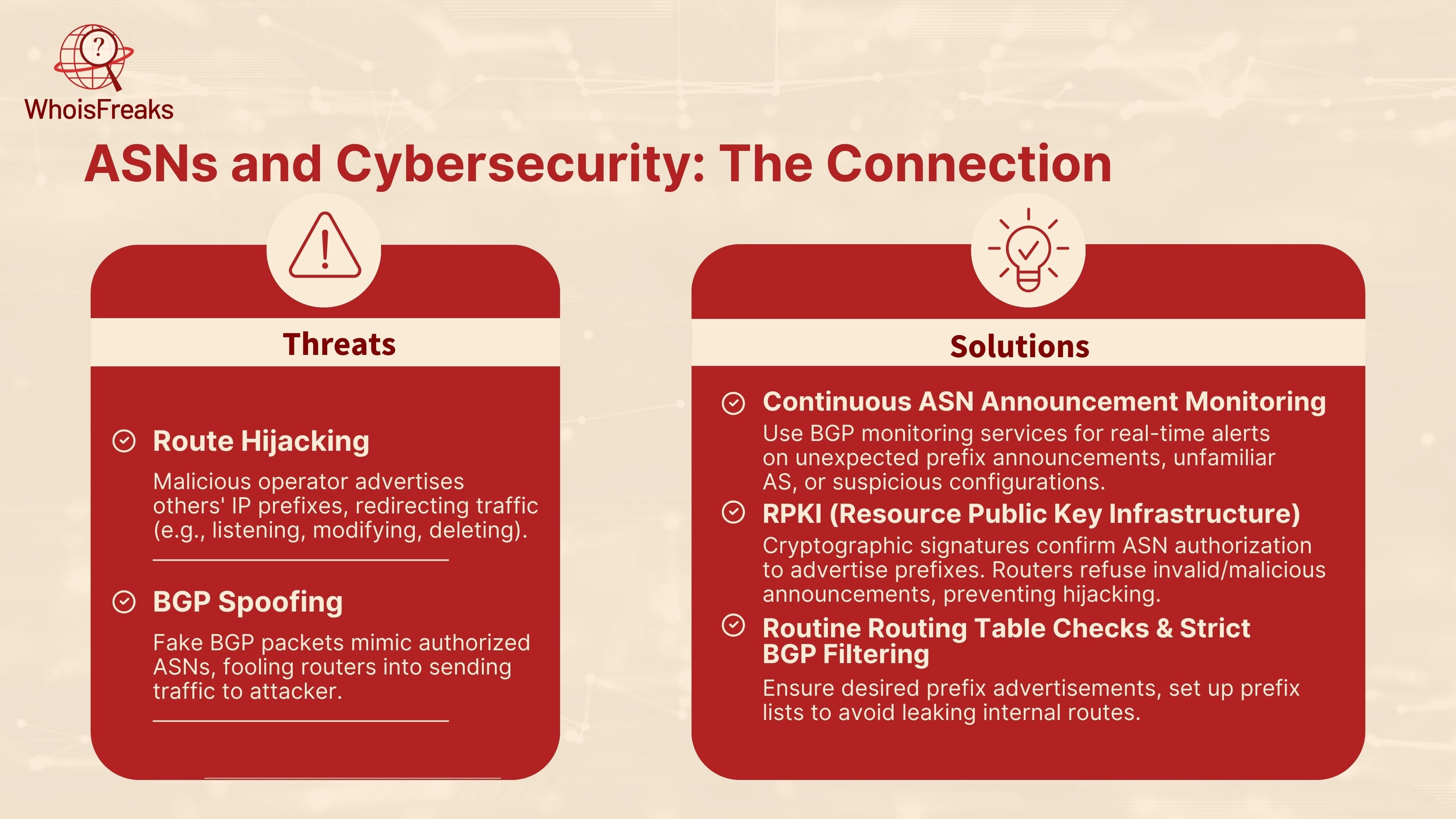
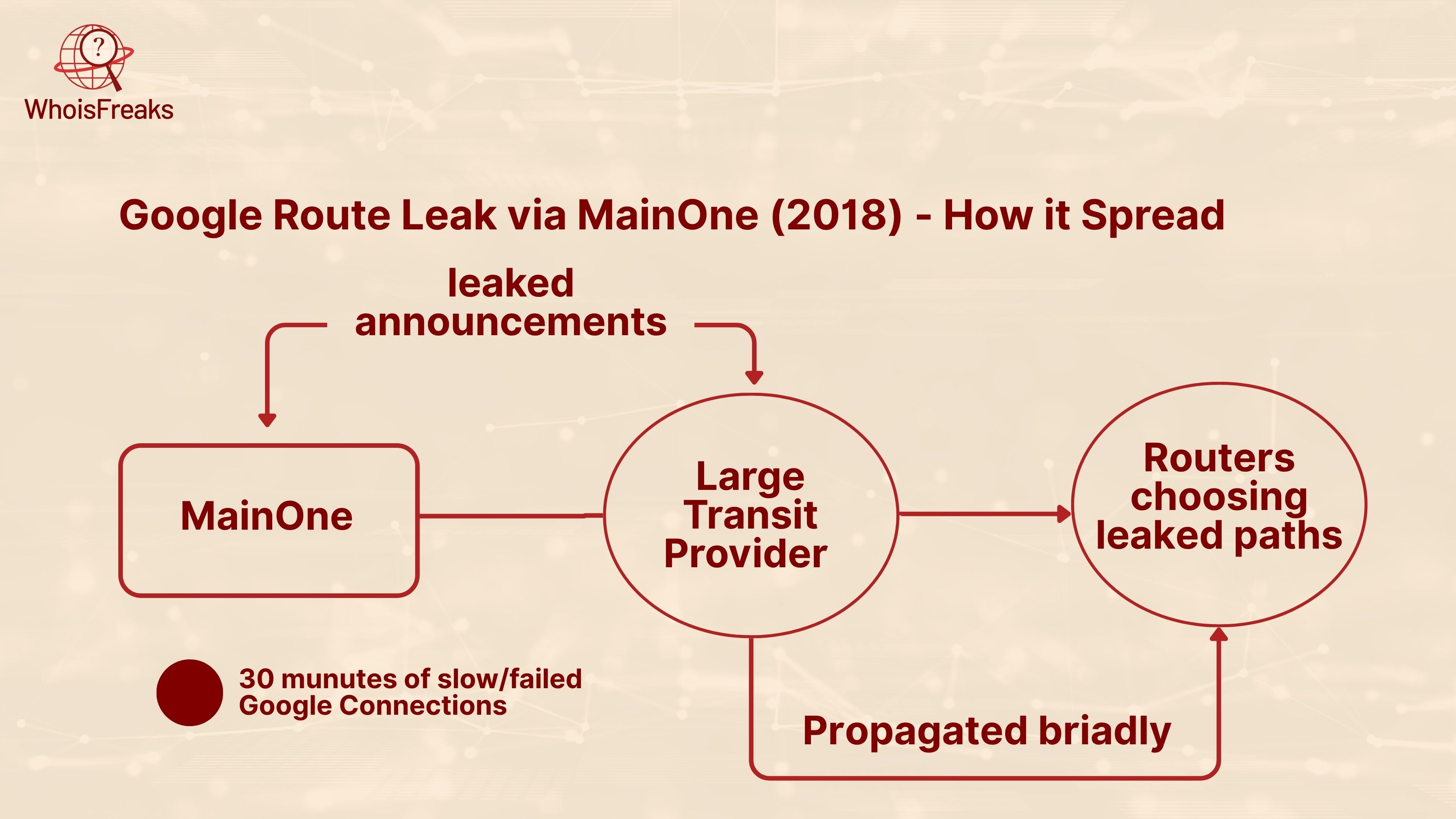
Route hijacking occurs when an unauthorized AS announces IP prefixes it does not own. Routers that accept the announcement begin sending traffic to the attacker's network instead of the legitimate destination. The 2008 YouTube outage caused by Pakistan Telecom (ASN 17557) and the 2018 Google route leak through Nigerian ISP MainOne are documented examples. Real-time BGP monitoring services alert network operators within seconds of an unauthorized prefix announcement.
Resource Public Key Infrastructure (RPKI) allows network operators to cryptographically bind an IP prefix to its authorized origin ASN using Route Origin Authorization (ROA) records. Routers that perform RPKI validation automatically reject BGP announcements from unauthorized origin ASNs. As of 2025, RPKI deployment has grown significantly, though adoption remains uneven across global carriers.
Threat intelligence platforms tag ASNs with reputation scores based on observed abuse. Analysts cross-reference incoming traffic's source ASN against these feeds to classify connections before applying policy. An IP originating from an ASN flagged in threat intel feeds warrants automated quarantine or manual review, while an IP from a known enterprise network warrants lower suspicion.
| Security Use Case | ASN Role | Action Taken |
|---|---|---|
| DDoS mitigation | Identify source ASN of attack traffic | Block IP prefix range at firewall or CDN |
| Threat attribution | Map IP to ASN owner and country | Classify traffic by operator and abuse history |
| Route hijacking detection | Monitor BGP announcements for unauthorized prefix claims | Alert NOC, coordinate with upstream to withdraw |
| WAF filtering | Apply ASN-based rules for data center and hosting ASNs | Block or challenge traffic from high-risk ASN categories |
| Phishing infrastructure | Trace phishing domain IP to hosting ASN | Identify bulletproof hosting providers and report abuse |
If you need a quick, web‑based ASN lookup no setup required check out the ASN Whois Lookup Tool from WhoisFreaks. Here’s what you get and how to use it for retrieving ASN information:

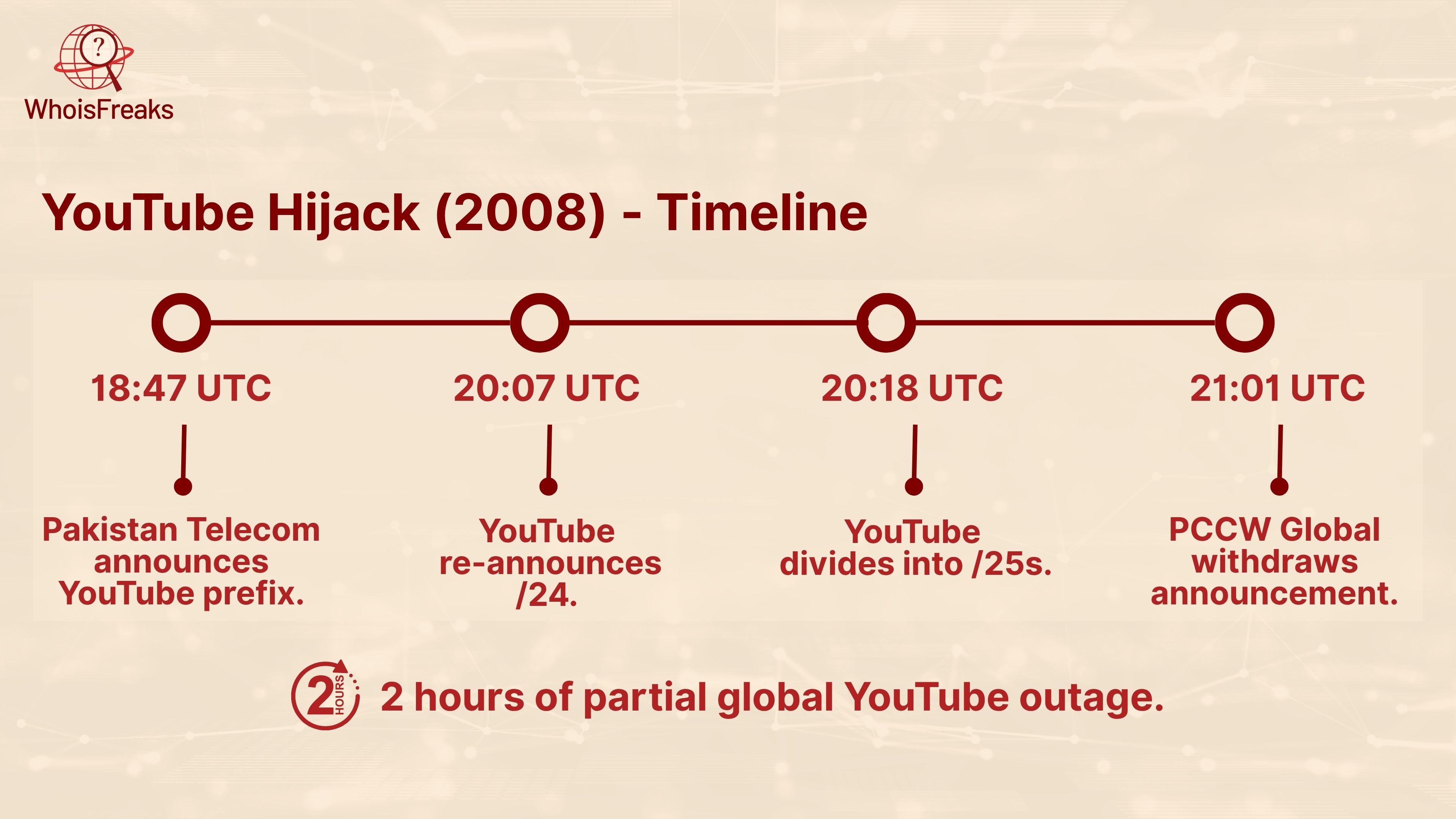
Pakistan Telecom (ASN 17557) unintentionally assigned the IP prefix of YouTube (208.65.153.0/24) as their own and all YouTube access throughout the world was then routed through Pakistan Telecom rather than Google network.
The Nigerian ISP MainOne misconfigured its BGP filters, exposing hundreds of prefixes owned by Google to its upstream providers including China Telecom. The traffic to Google services (Search, G Suite, YouTube) was redirected to the unexpected networks in China and Russia.
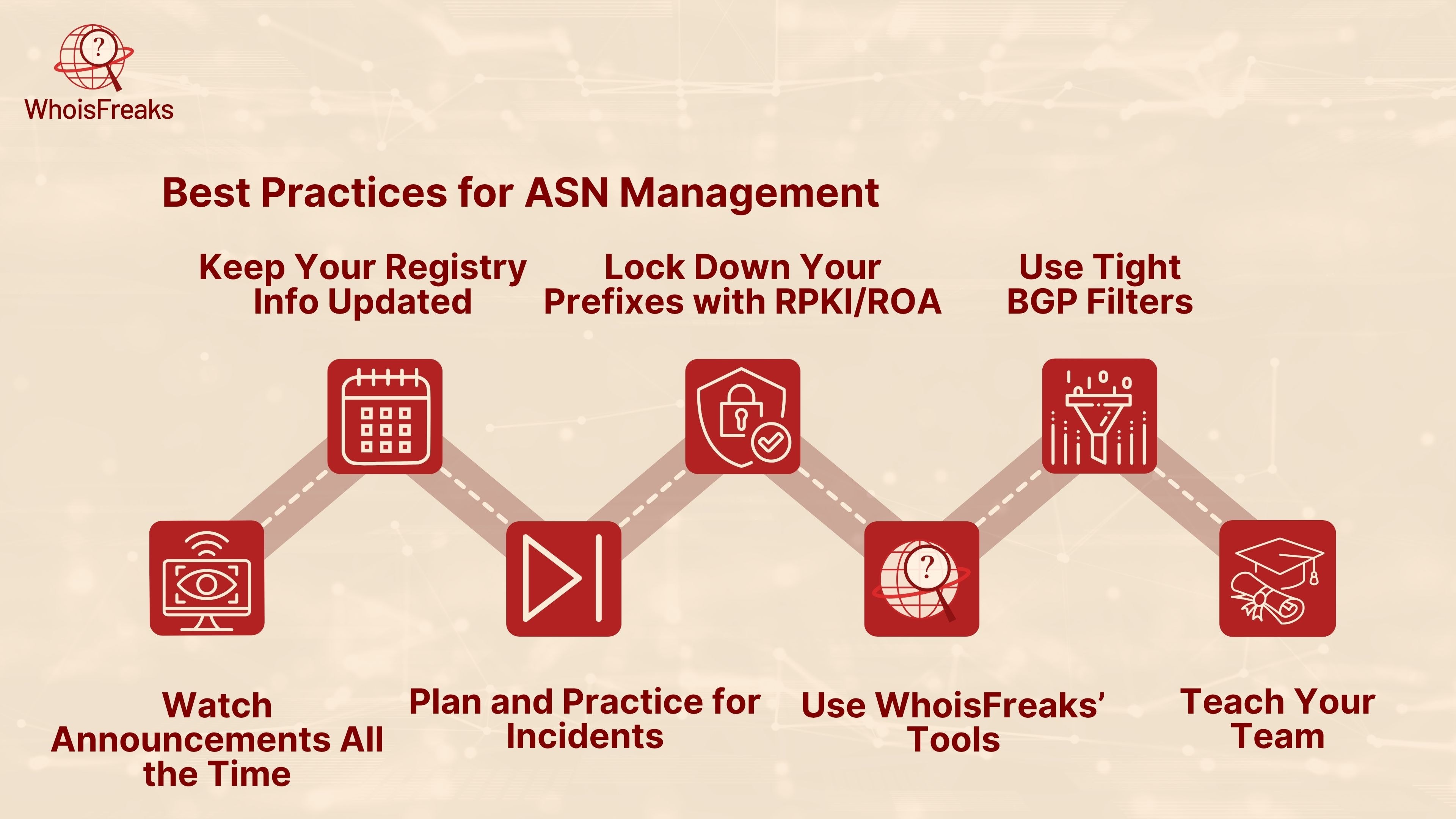
Keep your registry contact information current with your RIR. The abuse contact email on your ASN record is the address that upstream providers and other network operators use to reach you if your network is involved in a route hijack or becomes a source of malicious traffic. A stale or unreachable abuse contact delays incident response.
Publish ROA records for every IP prefix you announce. A ROA specifies which ASN is authorized to originate a given prefix. When your upstream providers perform RPKI validation, they will automatically reject invalid announcements of your address space. Start with your most critical prefixes and expand ROA coverage systematically.
Apply strict BGP outbound filters. Configure your routers to advertise only the IP ranges you legitimately own. Include explicit deny rules for private address ranges (RFC 1918) and unallocated space. BGP filtering prevents accidental route leaks that can disrupt other networks and damage your organization's routing reputation.
Maintain a written incident response plan for routing events. The plan should name your upstream provider's NOC contact, the process for requesting an emergency prefix withdrawal, and the internal escalation chain. Practice the procedure at least once per year. Route hijacking incidents unfold in minutes and require a practiced response.
Start ASN lookups when investigating unfamiliar source IPs in alert queues. The ASN tells you who operates the network, the country of registration, and the IP prefix range. This context helps you decide whether the IP warrants blocking, monitoring, or immediate escalation.
Cross-reference high-volume source ASNs against threat intelligence feeds. Some ASNs have persistent abuse records. Automating ASN reputation checks as part of your ingestion pipeline reduces manual triage time for known-bad network operators.
Bookmark a reliable ASN lookup tool for rapid incident lookups. The WhoisFreaks ASN Lookup tool at whoisfreaks.com/tools/asn-whois/lookup returns the owning organization, abuse contacts, IP prefix list, and BGP routing status for any ASN without requiring account creation. This is useful during active incident investigation when speed matters.
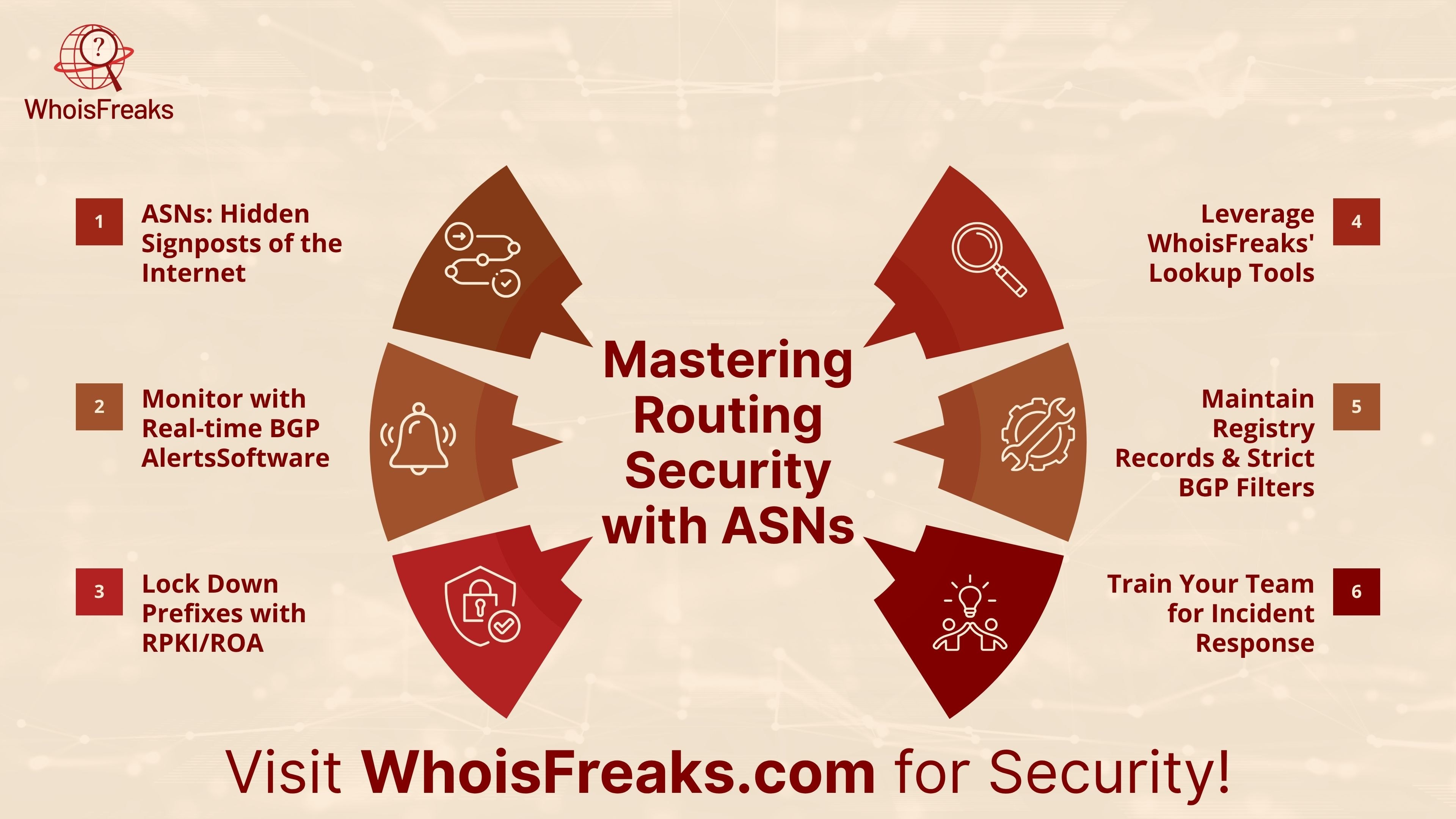
ASNs are the structural identifiers that give the internet its routing logic. For security teams, they are an intelligence layer that sits between a raw IP address and actionable attribution. Knowing which autonomous system an IP belongs to, who operates it, and what reputation it carries is a first-order pivot in any network investigation.
For organizations building automated threat pipelines or integrating ASN intelligence into SIEM workflows, the WhoisFreaks ASN Whois API provides programmatic access to real-time ASN records, including organization data, IP prefix lists, abuse contacts, and BGP routing status. See the ASN Whois API documentation for integration details.