
Blog
Combining WHOIS Data with DNS and SSL for Deeper Analysis Insights
Written By Qasim, WhoisFreaks Team Published: May 15, 2025, Last Updated: April 14, 2026

Blog
Written By Qasim, WhoisFreaks Team Published: May 15, 2025, Last Updated: April 14, 2026
When a suspicious domain appears in a threat feed, a security analyst does not look at WHOIS, DNS, and SSL data one source at a time. They look at all three together, because the signal that confirms or dismisses a threat usually lives in the gap between them.
A domain registered through a privacy proxy tells you very little. Add the DNS record showing it resolves to a shared IP block known for bulletproof hosting, then layer in an SSL certificate issued by an obscure CA three hours before the first observed attack traffic, and the picture becomes clear. That is the investigative technique this guide covers.
This post explains what WHOIS, DNS, and SSL data each reveal on their own, what each misses, and how to correlate all three for domain investigation, threat attribution, and infrastructure mapping. It is written for security analysts, threat intelligence teams, incident responders, and brand protection practitioners who need to move from a domain name to a complete infrastructure picture, fast.
The WhoisFreaks platform provides API access to WHOIS, DNS, and SSL data through separate endpoints that can be queried in sequence or in parallel, enabling the correlated analysis described in this guide.
Combining WHOIS, DNS, and SSL data gives investigators a three-layer view of any domain:
Analyzing all three together lets analysts detect discrepancies that no single source exposes alone, such as a domain registered through a privacy proxy (WHOIS), resolving to a fast-changing IP block (DNS), with a self-signed or recently issued certificate (SSL). That combination is a common signature of phishing, fraud, or C2 infrastructure.
WHOIS data is a public registry record tied to every registered domain. It is the first data source most investigators query because it establishes the ownership and temporal context of a domain before any active communication has occurred.
A WHOIS record contains several fields. Each has a specific investigative value:
| WHOIS Field | What It Contains | Investigative Signal |
|---|---|---|
| Registrar | The accredited registrar used to register the domain | Certain registrars are statistically over-represented in phishing and abuse cases |
| Creation Date | When the domain was first registered | Domains less than 30 days old at the time of first contact are high-risk |
| Expiration Date | When the registration lapses | Short registration windows (1 year or less) are common in throwaway infrastructure |
| Updated Date | Last modification to the record | Sudden updates can indicate ownership transfer or data falsification |
| Registrant Name/Org | Declared owner of the domain | Cross-reference with historical records; privacy protection may mask the real owner |
| Name Servers | DNS servers delegated to manage the domain | Shared name servers across multiple suspicious domains link infrastructure |
| Status Codes | EPP codes controlling domain operations | clientTransferProhibited is normal; unusual codes may indicate registry locks |
WHOIS shows who registered a domain and when, but it cannot confirm who currently controls the server, whether the content is malicious, or whether the SSL chain is valid. Those answers require DNS and SSL data.
Since GDPR implementation in 2018, many registrars redact registrant contact fields for European registrants and privacy-protected domains. When WHOIS contact data is masked, pivot to historical WHOIS records (available through the WhoisFreaks WHOIS History API) to check whether the registrant was ever publicly visible, and cross-reference shared name servers or registrar patterns to link domains to a common operator.
The Domain Name System (DNS) maps domain names to the servers that serve them. In an investigation, DNS records are not just routing data. They are infrastructure fingerprints.
Active DNS means querying a domain's current DNS records directly from authoritative servers. You get the answer the domain is serving right now.
Passive DNS means querying a database of historical DNS responses collected by resolvers over time. You get a record of every IP address, name server, and mail server the domain has pointed to, going back months or years.
For investigation purposes, passive DNS is more useful than active DNS because threat actors change infrastructure frequently to evade detection. A domain that resolves to 198.51.100.14 today may have resolved to 203.0.113.55 last week. That historical IP may already be on a blocklist or linked to known malicious infrastructure. Without passive DNS, that connection is invisible.
| Record Type | What It Contains | Investigative Use |
|---|---|---|
| A | IPv4 address the domain resolves to | Pivot to find other domains on the same IP (reverse IP lookup) |
| AAAA | IPv6 address | Same pivot potential as A records; less commonly monitored |
| MX | Mail server handling domain email | Shared MX records link domains to the same email infrastructure |
| NS | Name servers authoritative for the domain | Shared NS records are one of the strongest domain-clustering signals |
| TXT | Free-text records (SPF, DKIM, DMARC, etc.) | Absence of SPF or DMARC is common in newly registered phishing domains |
| CNAME | Alias pointing to another domain | CNAME chains can obscure the final hosting location |
| SOA | Start of Authority: zone management record | SOA serial numbers and TTL values can indicate rapid configuration changes |
Fast-flux is a technique used by threat actors to cycle through large pools of IP addresses for a single domain, typically with TTL values under 300 seconds. If passive DNS data shows a domain has resolved to dozens of different IP addresses over a short period, that is a strong indicator of botnet-controlled infrastructure. No single active DNS query would reveal this pattern.
SSL/TLS certificates have protected browser-to-server communications since the mid-1990s. The current standard, TLS 1.3 (RFC 8446, published August 2018), is the version in active use across virtually all modern HTTPS connections. SSL/TLS standards are maintained by the IETF. Certificate Transparency requirements for public trust are governed by the CA/Browser Forum Baseline Requirements, updated annually. When you visit a site with HTTPS (Hypertext Transfer Protocol Secure), SSL certificates are what make the connection secure.

An SSL certificate is a digital certificate that verifies a website's identity and creates an encrypted connection with the client. This encryption keeps any data exchanged, like personal or payment information, safe from hackers.
SSL/TLS certificates are issued by Certificate Authorities (CAs), which are trusted third-party organizations that verify domain ownership or organizational identity before signing a certificate. You can spot websites with valid certificates by the padlock icon in the browser's address bar and the "HTTPS" in the URL.
For cybersecurity experts or website owners, checking SSL certificate status is key. An expired certificate or one from a low-trust provider can leave a site open to man-in-the-middle attacks, where hackers intercept communications between the user and the site.
Every publicly trusted SSL/TLS certificate is required by browser policy to be logged in a Certificate Transparency (CT) log before it can be accepted by Chrome, Firefox, or Safari. CT logs are public, append-only records maintained by organizations including Google, Cloudflare, and DigiCert.
For investigation purposes, CT logs offer three capabilities that standard SSL checks do not:
Every certificate issued for subdomains of a domain appears in CT logs. A threat actor may register a domain and immediately issue certificates for login.domain.com, portal.domain.com, and webmail.domain.com. Each of those is a CT log entry. Querying CT logs against a root domain reveals the full certificate issuance history and every subdomain that has ever had a certificate, whether or not those subdomains currently resolve.
The timestamp of first certificate issuance is often earlier than the first domain contact in threat feeds. A certificate issued within hours of domain registration, especially for a domain with WHOIS privacy protection, is a strong early-warning signal.
The Certificate Authority that issued the certificate is logged. Legitimate enterprise domains use well-known CAs (DigiCert, Sectigo, Let's Encrypt for lower-assurance use cases). Domains using CAs with limited issuance history or unusual geographic origin warrant additional scrutiny.
CT log data can be queried through the WhoisFreaks SSL Lookup API, which returns the issuer, validity period, Subject Alternative Names (SANs), and issuance date for any domain's current and historical certificates.
While WHOIS data, DNS records, and SSL certificates are useful on their own, combining all three gives you a much deeper understanding of a website's infrastructure, security, and potential risks.
Individually, each component reveals important details for different organizations, but when combined, they provide a more complete picture. Here's how each part contributes to the bigger picture:
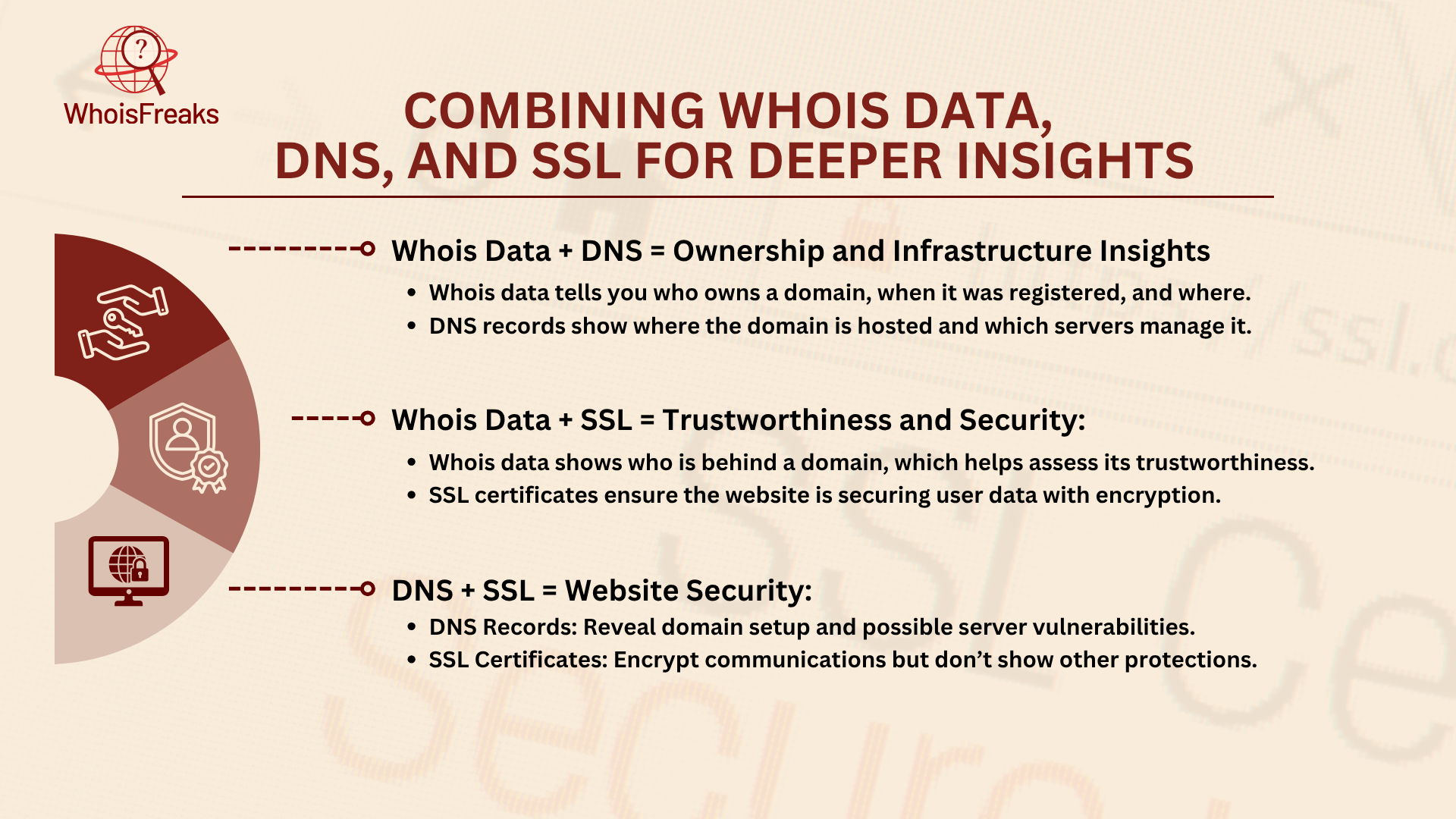
By comparing these two, you can identify discrepancies, such as a domain being owned by one entity but hosted on servers controlled by someone else. This can hint at third-party services or potential security risks from unknown servers.
Together, these datasets can help determine if a website is legitimate. For example, if a domain uses privacy protection for WHOIS data but lacks an SSL certificate, it might indicate a risky or fraudulent site.
By analyzing both, you can better assess website security. If the DNS records point to outdated servers and the SSL certificate is expired or from an unreliable provider, the site could be vulnerable to attacks.
The following workflow describes how to move from a suspicious domain name to a complete infrastructure assessment using all three data sources in sequence. Each step builds on the previous one.
Starting point: You have a domain name. It appeared in a phishing report, a threat feed, a brand alert, or a user complaint. You need to determine whether it is malicious, who operates it, and whether it is connected to other infrastructure you should be tracking.
Query the WHOIS record for the domain using the WhoisFreaks WHOIS lookup tool or the WHOIS API endpoint. Note: creation date, registrar, registrant name or organization (if not privacy-protected), name servers, and expiration date.
Check for these risk signals:
If name servers are shared with other known-bad domains, you have already found a cluster. For a full walkthrough of how analysts pivot between domains using shared registrant attributes, see the guide to reverse WHOIS for threat hunting.
Pull the A, MX, NS, and TXT records for the domain. Then query passive DNS if available to see the full history of IP resolutions.
Check for:
Query the SSL certificate for the domain. Note: the issuer CA; the issuance date relative to the domain creation date; the Subject Alternative Names (SANs) listed in the certificate; and the CT log history.
Check for:
| Signal Combination | Interpretation |
|---|---|
| WHOIS privacy + new registration + fast-flux A record + Let's Encrypt cert | High-risk: likely phishing or malware delivery |
| Shared NS with known-bad domains + no MX record + expired cert | Infrastructure pivoting: connected to known actor |
| Long-established WHOIS + stable A record + EV or OV certificate | Lower risk: consistent with legitimate operation |
| WHOIS privacy + stable A record + valid cert from major CA | Ambiguous: privacy-conscious but not immediately suspect |
| New registration + shared hosting IP + no SPF/DMARC + Let's Encrypt cert | Medium risk: monitor; may be newly launched legitimate site |
WhoisFreaks provides separate API endpoints for WHOIS lookup, DNS record retrieval, and SSL certificate data, all returning structured JSON. For an automated investigation pipeline, query all three in sequence for each domain. The API returns structured JSON, which can be parsed directly into a SIEM, threat intelligence platform, or custom investigation tool. The WhoisFreaks Domain Monitoring product can alert you when any of these records change for a domain you are tracking.
WHOIS data, DNS records, and SSL certificates offer more than just security benefits; they can also provide valuable resources that give businesses a competitive edge. By using these data sources, companies can make smarter decisions, monitor competitors, and discover new opportunities for growth.
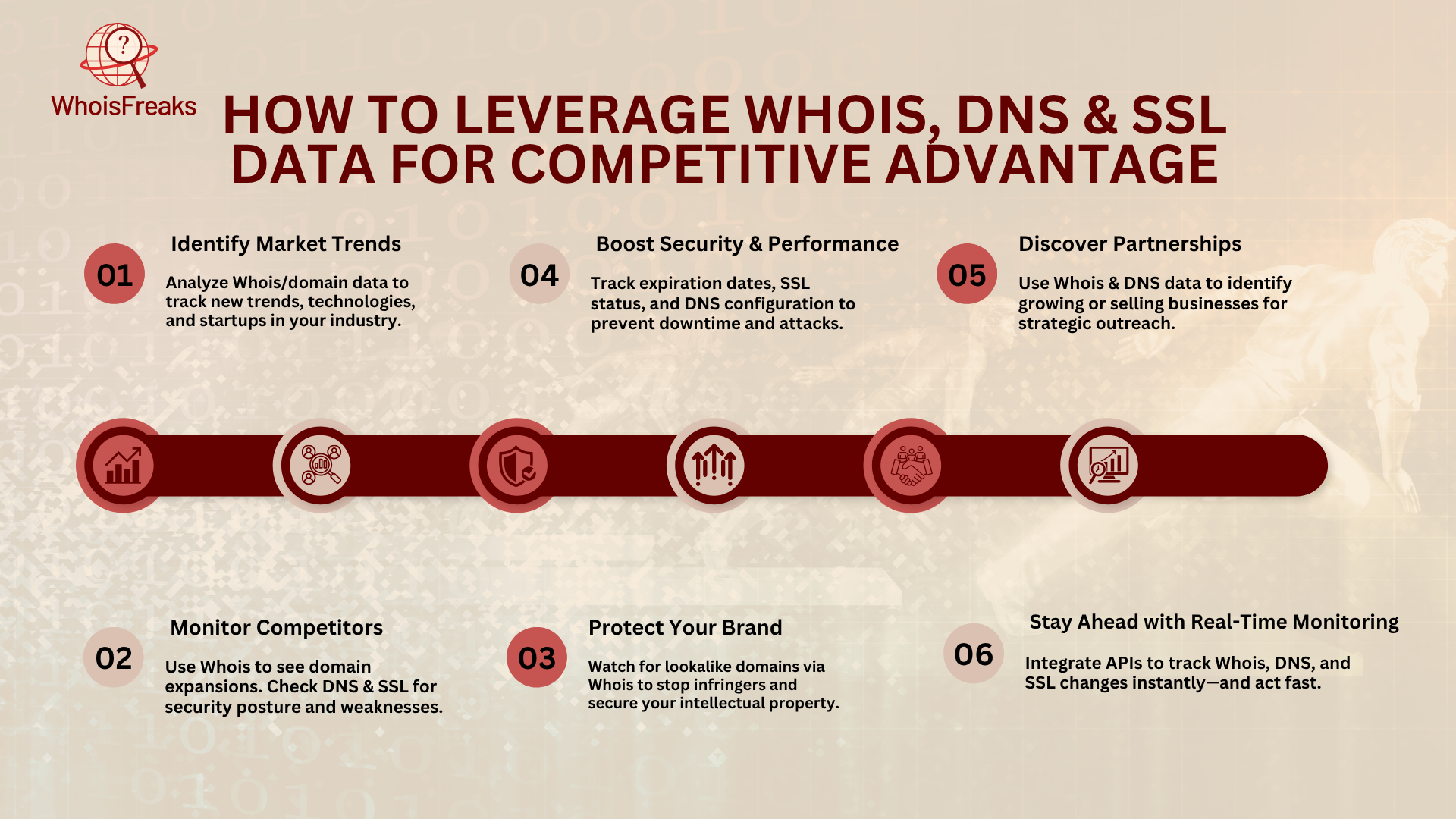
By analyzing WHOIS and domain data, businesses can spot emerging trends and new opportunities. For example, new domains in your industry could signal a shift toward new technologies or services, which you can take advantage of. Monitoring WHOIS records also helps you discover startups entering your niche, giving you a chance to position yourself early or form partnerships. You can even find other domains owned by the same company to learn about their online presence and where you might outperform them.
Tracking competitors' domains, DNS records, and SSL certificates gives you valuable insights into their strategies. WHOIS data can show if they are expanding their digital presence, while DNS and SSL records tell you how secure their websites are. If a competitor's SSL certificate is expired or weak, you can use it as an opportunity to highlight your own stronger security, making your website seem more trustworthy.
Monitoring WHOIS data for domains similar to yours helps protect your brand from potential infringers or domain squatters. If you spot suspicious domain names that are similar to your own, you can act early by purchasing those domains or filing for trademark protection. This helps prevent others from taking advantage of your brand and ensures your intellectual property is secure.
By checking your domain's expiration dates and SSL certificate status regularly, you can avoid interruptions and maintain a secure website. Reviewing DNS records ensures your website is properly configured and safe from attacks. A strong SSL certificate not only secures your site but also boosts your SEO, builds trust with users, and sets you apart from competitors who may neglect these security aspects.
WHOIS and DNS data can help you spot businesses that might be open to partnerships or acquisitions. By checking WHOIS records, you can find companies that are selling domains or expanding their online presence. This gives you an early opportunity to reach out for partnerships or explore acquisitions that can help grow your business.
Real-time monitoring of WHOIS, DNS, and SSL data is key to staying competitive. Using APIs, you can track changes like domain ownership shifts or SSL certificate renewals as they happen. This allows you to quickly react to changes in your competitors' strategies and stay ahead in the market.
To make the most of WHOIS data, DNS records, and SSL certificates, it's crucial to establish a routine monitoring strategy. Regularly reviewing these elements helps keep your domains secure, identify potential threats, and stay ahead of competitors. Here are some best practices to follow:
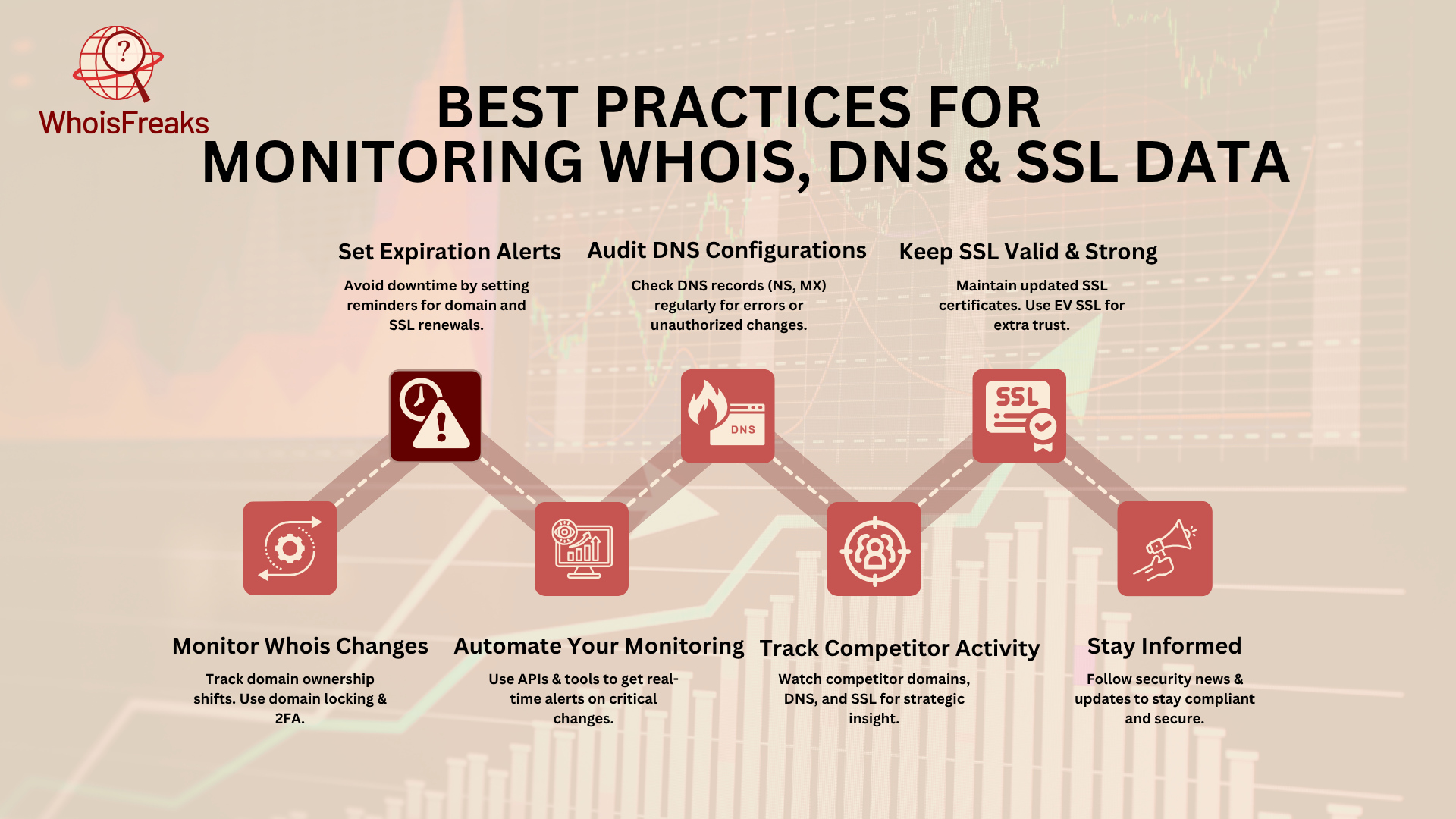
Set expiration alerts for both domain registration and SSL certificates. Thirty days is the minimum lead time for SSL renewals; for domains, ninety days gives enough time to troubleshoot registrar issues. Let these alerts run automatically. Missed renewals are one of the most preventable causes of security incidents.
Ensure your DNS records are correct and secure to prevent downtime or security breaches. Regularly check your Name Server (NS) and Mail Exchange (MX) records. Make sure your DNS resolution is working as expected and be on the lookout for any unauthorized changes or issues.
Always have a valid SSL certificate to ensure secure connections and improve SEO. Regularly check the expiration date and use tools like SSL Labs to verify the certificate's strength. Extended Validation (EV) certificates provide the highest level of organizational verification. Note that major browsers including Chrome (since 2019) no longer display the EV organization name in the address bar, so EV certificates primarily serve compliance and internal trust requirements rather than visible trust signals for end users.
Track changes in WHOIS records to spot ownership or registration shifts. Unauthorized changes may signal a cyberattack or security threat. Ensure your domain registrar is reputable and use extra protection features like two-factor authentication and domain locking to safeguard your domain.
Given the volume of data to monitor, automation is essential for your ability to efficiently track changes. Use APIs for continuous DNS and WHOIS record monitoring and get alerts for any critical changes. SSL monitoring tools can also track your certificates and notify you if they're about to expire or need reconfiguration.
Monitor your competitors' WHOIS, DNS, and SSL data, including domains registered, to stay informed on their strategies and security posture. Set up alerts for domain changes, check if their SSL encryption is up to standard, and track their DNS records for any security vulnerabilities. This can give you an edge by identifying their weaknesses.
Stay current with industry changes by following security blogs, subscribing to bulletins, and keeping up with ICANN regulations. Be aware of updates to SSL standards to ensure your website is always meeting the latest security protocols.
WHOIS, DNS, and SSL data each capture a different layer of domain identity. The combination of all three is what lets analysts see what no single source reveals: the ownership, infrastructure, and trust posture of a domain at the same time. Use the five-step workflow above as your baseline investigation sequence, and the WhoisFreaks API to automate it at scale.

DNS spoofing redirects users to malicious sites by injecting false DNS records. Learn how it works, how to detect it, and how DNSSEC stops it.
14 min read
Learn what SSL/TLS certificates are and why they are essential for website security and data protection.
6 min read