
Blog
SPF DKIM DMARC Explained: The DNS Trio That Secures Your Emails
Written By Qasim, WhoisFreaks Team Published: May 21, 2025, Last Updated: February 25, 2026

Blog
Written By Qasim, WhoisFreaks Team Published: May 21, 2025, Last Updated: February 25, 2026
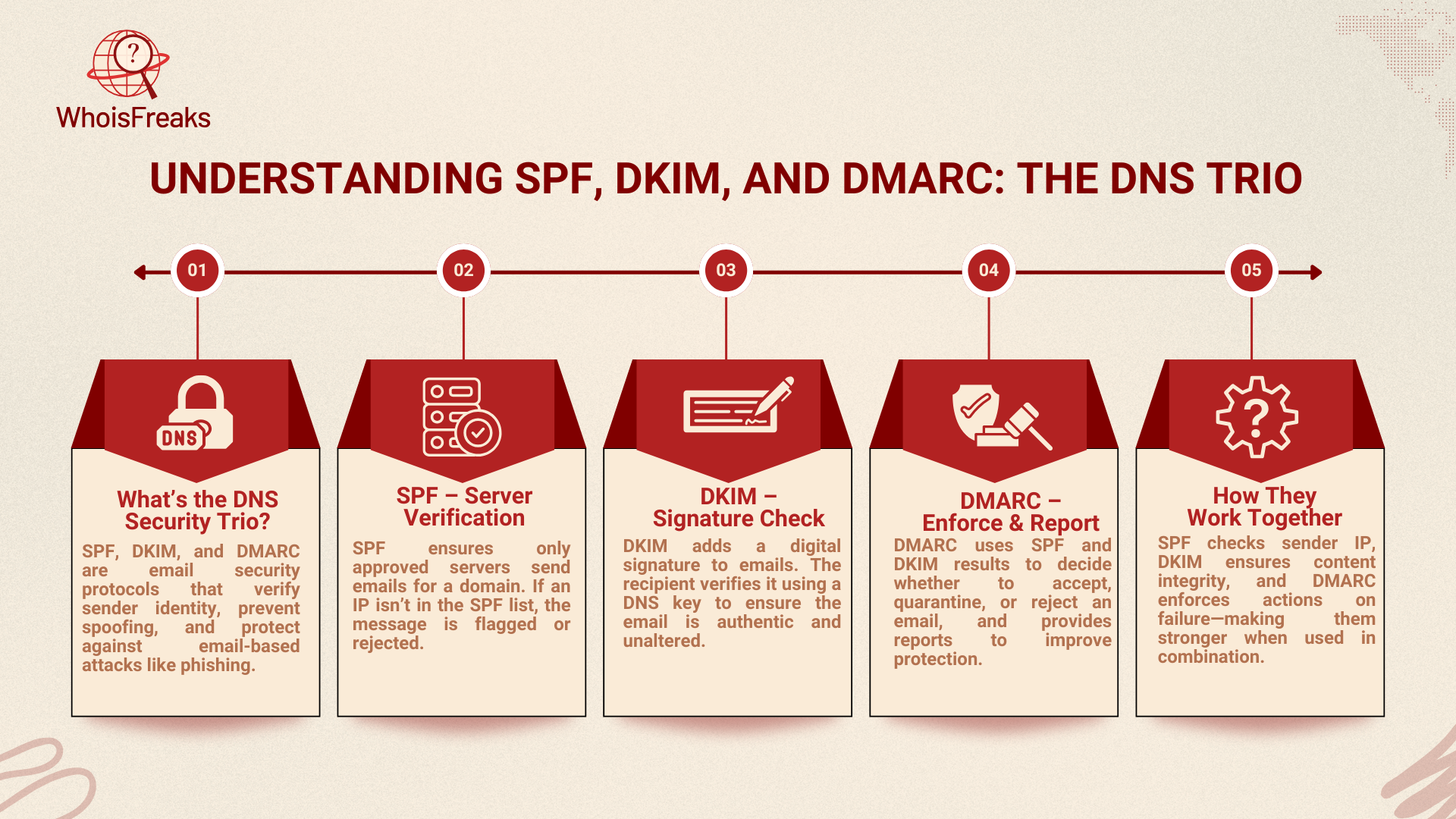
Email security is a major concern for individuals and businesses today, especially for email servers. With phishing, domain spoofing email spoofing, and fraud on the rise, it's crucial to ensure that emails are legitimate and secure. One of the best ways to protect email communication is through authentication protocols like SPF, DKIM, and DMARC. These three protocols, known as the "DNS Trio" work together to confirm that emails are authentic, preventing unauthorized users from impersonating legitimate senders.
Whether you're an IT professional, business owner, or email service providers, it's important to understand how SPF, DKIM, and DMARC function. These protocols help secure emails, boost deliverability, and guard against spoofing, which can damage your reputation and lead to serious security risks.
In this blog, we’ll explain what SPF, DKIM, and DMARC are, how they work, and why they’re crucial for securing your emails. We’ll also share tips on how to set them up for your domain and improve your email security strategy.
SPF, DKIM, and DMARC are essential email security protocols that work together to authenticate and protect email messages. These protocols ensure that the emails you send and receive come from trusted sources, preventing attackers from impersonating your domain or tampering with your email content.
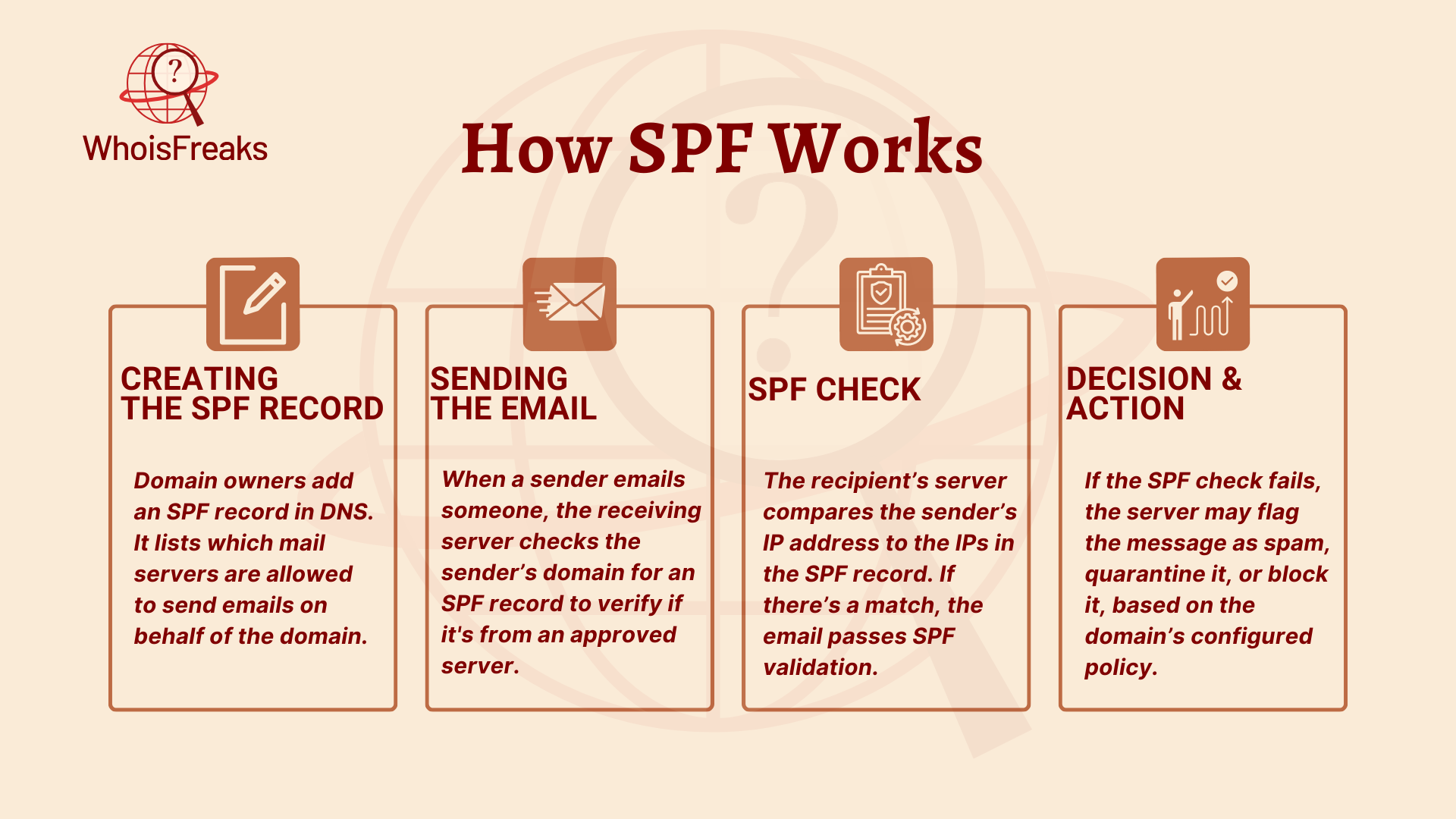
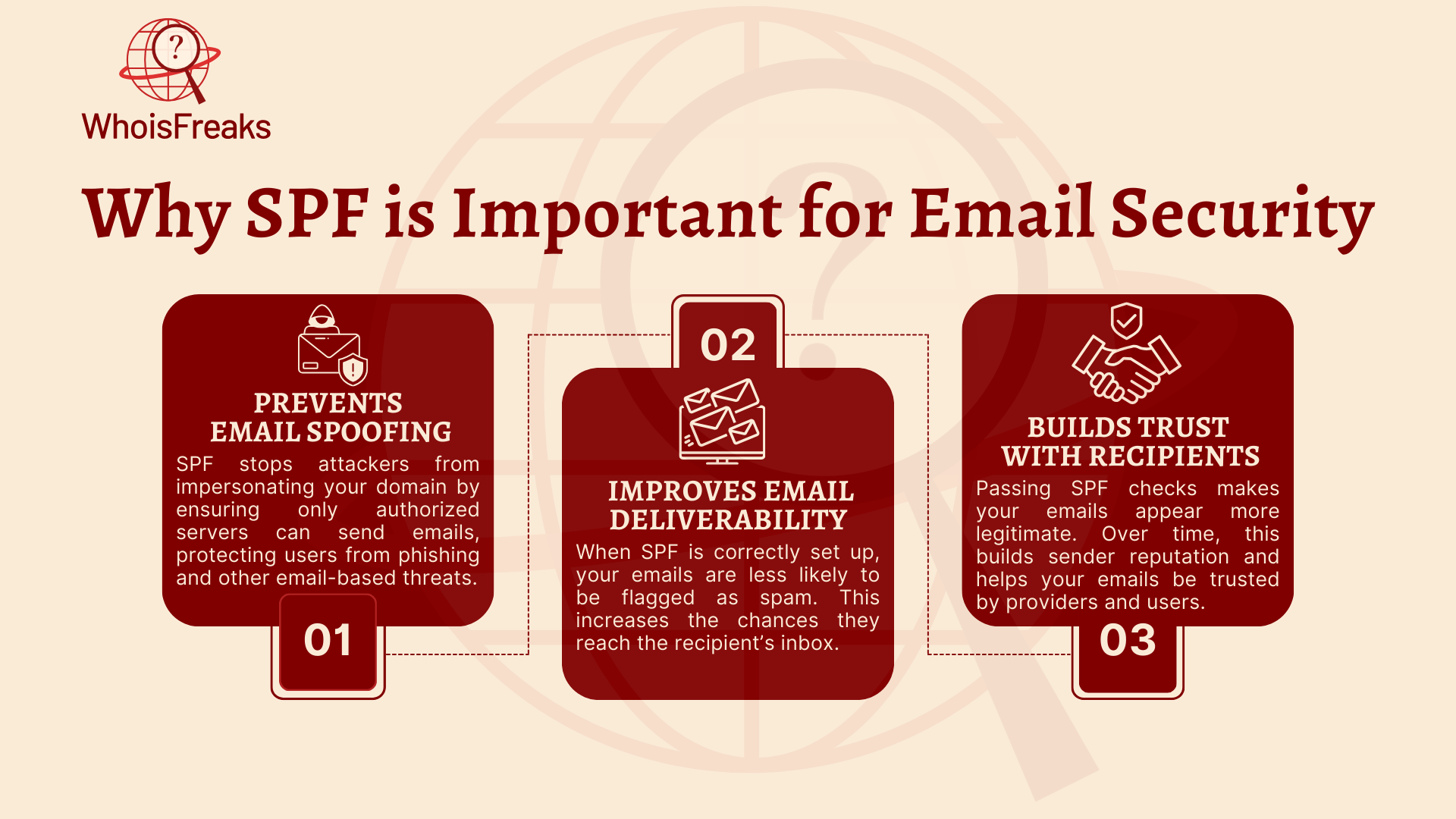
The Sender Policy Framework (SPF) is an essential email authentication protocol that helps prevent email spoofing. It allows domain owners to specify which mail servers are authorized to send emails on their behalf, preventing unauthorized senders from impersonating your domain. This is crucial for protecting your brand and ensuring that legitimate emails reach their intended recipients.
SPF is a protocol that validates the sender’s IP address by checking it against a domain’s SPF record, which is stored in DNS (Domain Name System). This record lists the mail servers that are authorized to send emails for the domain. When an email is sent, the receiving mail server checks the SPF record. If the sender's IP address matches one of the authorized addresses, the email is deemed legitimate. If not, the email is flagged as suspicious or rejected.
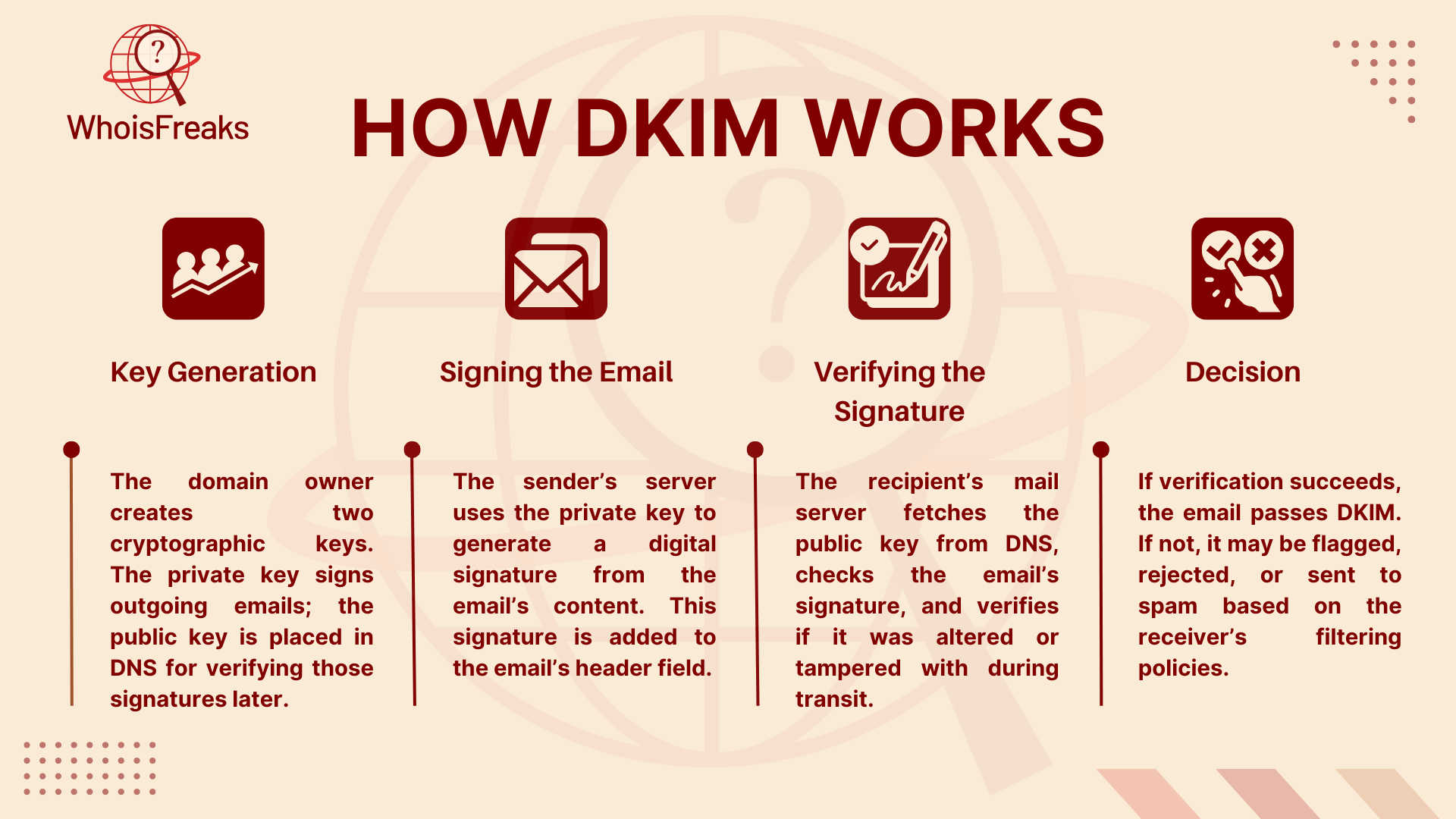
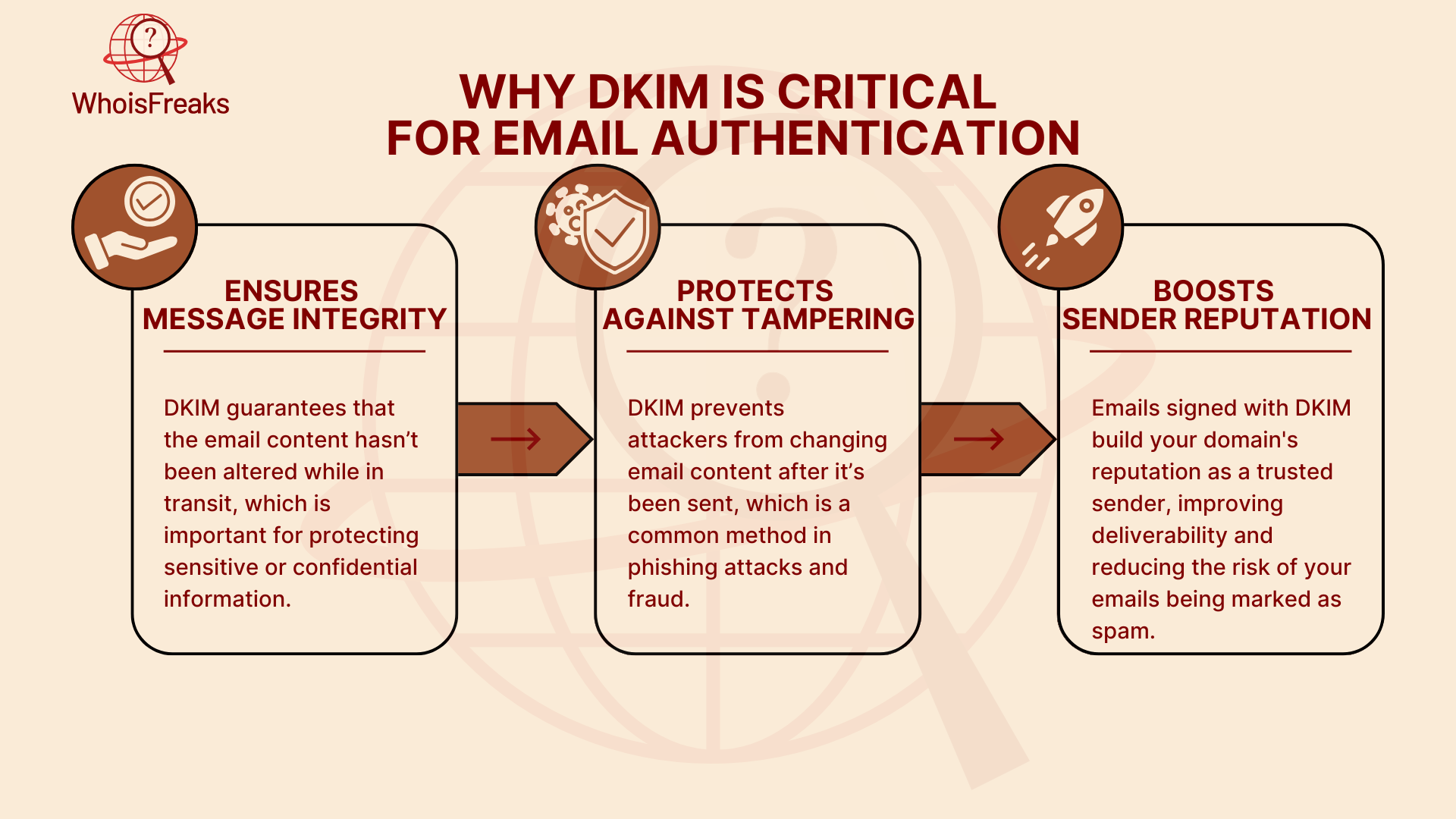
DomainKeys Identified Mail (DKIM) is another essential email authentication protocol that ensures both the integrity and authenticity of email messages. While SPF focuses on validating the sender's server, DKIM adds an extra layer of security with DKIM authentication by digitally signing emails. This digital signature confirms that the email content hasn’t been altered and that it truly came from the domain it claims to originate from.
DKIM works by attaching a unique digital signature to the email’s header. This signature is created using a private key that only the sender's mail server holds. When the email is received, the recipient’s mail server checks the DKIM signature against a public key stored in the domain's DNS records. If the public key matches, the email is deemed authentic and unaltered.
The DKIM signature contains the following information:
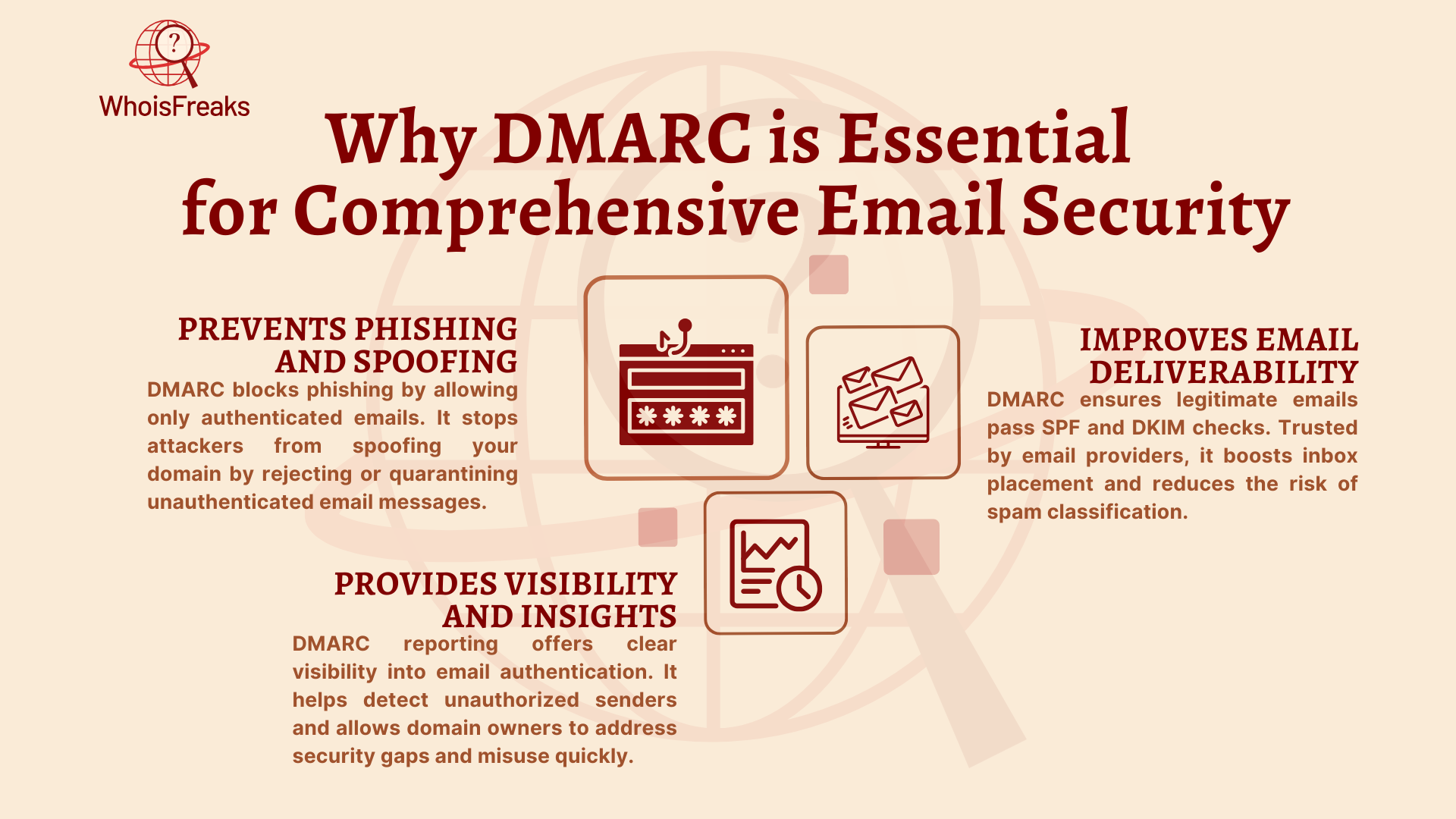
DMARC is the third and final piece of the email authentication trio. While SPF and DKIM verify the legitimacy of the sending server and the integrity of the email message, DMARC ties these two protocols together and provides domain owners with a policy to dictate how to handle unauthenticated emails. By implementing DMARC, domain owners can enforce email authentication policies, ensure email security, and improve their overall email deliverability.
DMARC is the final piece of the email authentication puzzle. While SPF and DKIM verify the sender’s server and the integrity of the email, DMARC combines both and lets domain owners set policies on how to handle unauthenticated emails. By implementing DMARC, domain owners can enforce authentication policies, improve email security, and enhance email deliverability.
To provide a clearer understanding of how SPF, DKIM, and DMARC work together to secure email communication, here’s a comparison table that highlights the key differences and benefits of each protocol:
| Feature | SPF (Sender Policy Framework) | DKIM (DomainKeys Identified Mail) | DMARC (Domain-based Message Authentication, Reporting & Conformance) |
|---|---|---|---|
| Purpose | Verifies the sending mail server | Ensures the integrity of the email message | Combines SPF and DKIM to enforce authentication and reporting |
| Mechanism | Checks if the sender's IP address matches authorized IPs in DNS | Uses a digital signature to verify the email’s integrity and authenticity | Uses SPF and DKIM results to enforce policies and send reports |
| DNS Records | SPF record in DNS | DKIM public key in DNS | DMARC policy in DNS |
| Primary Benefit | Prevents email spoofing at the sender’s server level | Confirms that the email content hasn’t been altered during transit | Provides a policy for handling unauthenticated emails and sends reports |
| Common Use | Prevents unauthorized servers from sending email on behalf of the domain | Ensures the authenticity and integrity of the email content | Protects the domain from phishing and spoofing while improving deliverability |
| Action on Failure | Fails the check if the IP doesn’t match the domain's SPF record | Fails if the digital signature doesn’t match the public key in DNS | Can quarantine, reject, or report emails that fail authentication checks |
Setting up SPF, DKIM, and DMARC helps secure your domain’s email and improves deliverability. Here's how to set them up:
v=spf1 ip4:<Authorized_IPs> include:<Third_Party_Services> ~all
default._domainkey.yourdomain.com IN TXT "v=DKIM1; k=rsa; p=<Your_Public_Key>"
_dmarc.yourdomain.com IN TXT "v=DMARC1; p=none; rua=mailto:[email protected]; ruf=mailto:[email protected]; pct=100"
DNS records are crucial for the operation of email authentication protocols like SPF, DKIM, and DMARC. These DNS txt record ensure that only legitimate emails are delivered and help protect your domain from email spoofing and phishing attacks. By configuring the correct DNS records, you can ensure that your email system is secure and trustworthy.
Key DNS records like TXT, MX, and CNAME play an essential role in email security. These records define the rules for SPF, DKIM, and DMARC in your domain's DNS settings, making sure that emails are properly authenticated and delivered to the intended recipient. TXT records are used to store SPF and DMARC data, MX records determine which mail servers handle email for your domain, and CNAME records are used for DKIM public key lookups in DNS.
Accurate DNS configuration is essential to ensure email authentication functions correctly. Proper configuration helps protect against spoofing, improves email deliverability, and provides visibility into the authentication process. Mistakes in DNS records can lead to email delivery failures, such as legitimate emails being flagged as spam or even rejected outright. To maintain email security, it is important to regularly update your DNS records and monitor them for errors. Monitoring tools can help you detect issues with your authentication records. Additionally, implementing DNSSEC (Domain Name System Security Extensions) enhances security by protecting your DNS records from tampering and unauthorized changes.
Email spoofing happens when attackers send emails that look like they come from a trusted source, but they’re actually from a different, fake server. This is often used for phishing attacks, tricking people into giving away sensitive information like passwords or credit card numbers. Spoofing can also damage your brand’s reputation and make people distrust your emails.
Email deliverability is the ability of your emails to reach the recipient’s inbox instead of getting sent to the spam folder or rejected. Poor deliverability can hurt communication, whether you're sending marketing emails, transaction updates, or personal messages. Factors like sender reputation, spam filters, and being blacklisted can affect deliverability.
SPF, DKIM, and DMARC improve email deliverability from the sender's domain:
By using SPF, DKIM, and DMARC, you can protect your emails from spoofing and improve the chances that your real emails will pass authentication checks and reach their destination safely.
Securing your email communication is more important than ever. With the increasing threats of email spoofing, phishing, and other cyberattacks, protocols like SPF, DKIM, and DMARC provide essential layers of protection to safeguard your domain and improve email deliverability. By understanding and correctly implementing these protocols, you can ensure that your emails are authenticated, trusted, and secure.
Implementing SPF, DKIM, and DMARC not only protects your domain from impersonation but also improves the trustworthiness of your email communication. These protocols verify that the emails you send are from legitimate sources, ensure that email content remains untampered with during transit, and help protect your reputation. More importantly, they provide an effective defense against phishing and spoofing attacks, which can have devastating effects on your business and personal security.
As you move forward with securing your email systems, the next steps are crucial. Begin by implementing email authentication setting up SPF, DKIM, and DMARC for your domain. Start with configuring your SPF records to specify authorized mail servers, then proceed with DKIM to sign your emails for integrity verification and finally implement DMARC to enforce policies on how your emails are handled by receiving servers. By following these steps, you’ll enhance your email security and significantly reduce the chances of unauthorized actors exploiting your domain.
To ensure the ongoing success of your email security strategy, regularly monitor your SPF, DKIM, and DMARC records, analyze reports, and adjust your configurations as needed. Over time, as you gain confidence in your email authentication method setup, you can move to stricter DMARC policies for enhanced protection. Implementing these measures may take some time and effort, but the long-term benefits of a secure, trustworthy email environment are invaluable for your business or personal communication.

Discover essential insights on DNS poisoning and learn practical steps to safeguard your online presence. Read the article for vital protection tips.
9 min read

Learn how a DNS flooder can threaten your network security and discover practical measures to protect your systems. Read more to safeguard your network.
9 min read

Discover the essential role of DNS servers in internet functionality and learn how they enhance your online experience. Read the article for insights.
11 min read