
Blog
Confronting the Dark Side of WHOIS Common Abuse and How to Prevent It
Written By Qasim, WhoisFreaks Team Published: May 16, 2025, Last Updated: April 13, 2026

Blog
Written By Qasim, WhoisFreaks Team Published: May 16, 2025, Last Updated: April 13, 2026
WHOIS abuse refers to the unauthorized or unethical exploitation of domain registration data to extract contact details for spam campaigns, facilitate phishing attacks, enable domain hijacking, or conduct unauthorized surveillance. Because WHOIS records were designed for transparency, their open structure makes them a persistent target for actors who treat public registration data as a harvesting opportunity rather than an accountability mechanism.
WHOIS is a query-and-response protocol (standardized in RFC 3912) that registrars and registries use to publish domain registration records, including registrant contact information, registration and expiration dates, name servers, and registrar identity. Created in 1982 as RFC 812 and widely deployed to help network administrators resolve infrastructure problems, WHOIS was built on the assumption that domain registrants would provide accurate data and that public access would be constrained to legitimate operational purposes.
That assumption has not held. Security researchers, legal teams, and brand protection analysts now faces an ecosystem where the same data designed for accountability is systematically harvested for spam, phishing, identity theft, and domain hijacking. GDPR and similar privacy regulations have restricted public access to WHOIS records since 2018, but this has created a new problem: legitimate investigators struggle to access data that was previously available, while well-resourced threat actors route around redactions using bulk registration tactics and proxy services.
This article covers the most common forms of WHOIS and domain abuse, the regulatory environment shaping WHOIS access, and the concrete technical and procedural measures that security teams, domain owners, and brand protection analysts can apply today.
Domain abuse is the use of a registered domain name for purposes that violate registrar terms of service, applicable laws, or broadly accepted internet norms. The forms it takes are not uniform: a domain abusing actor might register a lookalike domain to intercept credentials, operate a bulk registration scheme to harvest WHOIS data, or park a domain with malware redirects while hiding behind WHOIS privacy services.
ICANN classifies the five primary categories of domain abuse as: phishing, malware distribution, spam, botnets, and pharming. A 2013 ICANN-commissioned study on WHOIS privacy and proxy service abuse found that among domains associated with advanced fee fraud, 46% used WHOIS privacy or proxy services to conceal registrant identities, hampering law enforcement and registrar abuse teams trying to act on complaints.
WHOIS abuse is a specific subset of domain abuse. Where domain abuse describes what the domain is used for, WHOIS abuse describes misuse of the registration data itself: scraping contact fields to build spam lists, using registrar login credentials obtained via WHOIS enumeration to initiate unauthorized transfers, or constructing targeted phishing lures using registrant name, address, and email data pulled directly from the public record.
Understanding this distinction matters operationally. A domain abuse response typically involves a registrar takedown request or UDRP filing. A WHOIS abuse response may instead require a data protection complaint, a cease-and-desist to the harvesting party, or technical rate-limiting measures on WHOIS query endpoints.
WHOIS is a query-and-response protocol defined in RFC 3912, published by the Internet Engineering Task Force (IETF) in 2004. It replaced the earlier RFC 954 (1985) and RFC 812 (1982), which first formalized how network administrators could retrieve information about IP address assignments and domain name registrations.
At the protocol level, WHOIS works as a simple TCP request on port 43. A client sends a plain-text query (a domain name or IP address) to a WHOIS server, and the server returns a structured plain-text response. There is no authentication, no encryption, and no rate-limiting built into the protocol itself; those controls are implemented by individual registrars and registries at their discretion.
The data returned in a WHOIS response for a registered domain typically includes: the registrant organization name and contact details, administrative and technical contact records, the registrar of record, domain creation, update, and expiration dates, name server assignments, and the domain's status codes (such as clientTransferProhibited).
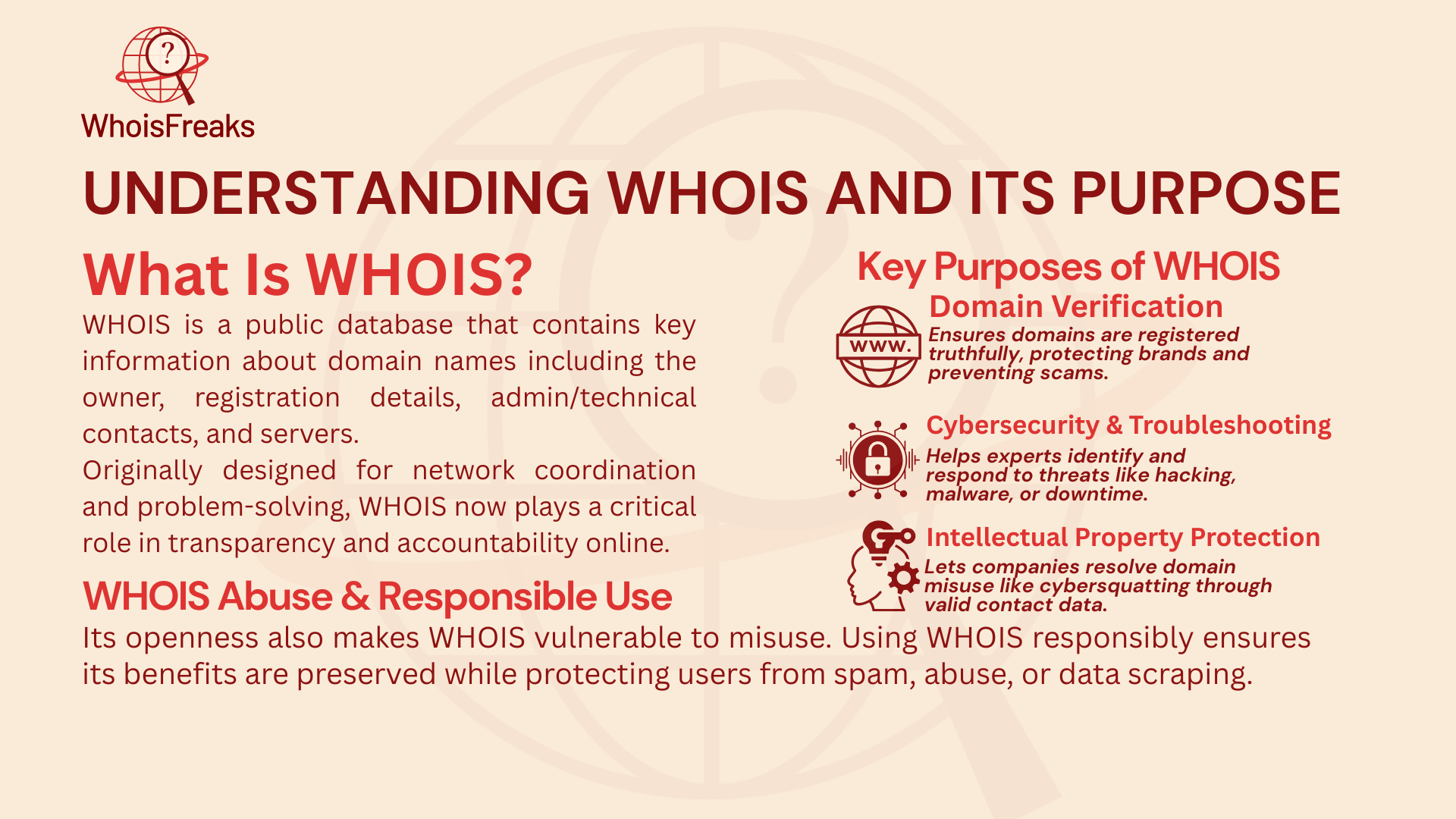
WHOIS was built to serve three operational purposes.
These three purposes remain valid. The conflict today is that the same open-access design that makes WHOIS useful for legitimate investigations also makes it a rich target for automated harvesting, credential-extraction attacks, and surveillance.
RDAP (Registration Data Access Protocol), standardized in RFC 7483, is WHOIS's successor. It returns structured JSON responses rather than plain text, supports role-based access for credentialed users such as law enforcement and security researchers, and includes built-in privacy controls that comply with GDPR requirements. Most major registries now operate parallel RDAP endpoints.
Even though WHOIS is a useful tool, it has also become a goldmine for bad actors. That’s why it’s so important to know about the most common kinds of WHOIS abuse. Here’s a look at the biggest and most harmful types:
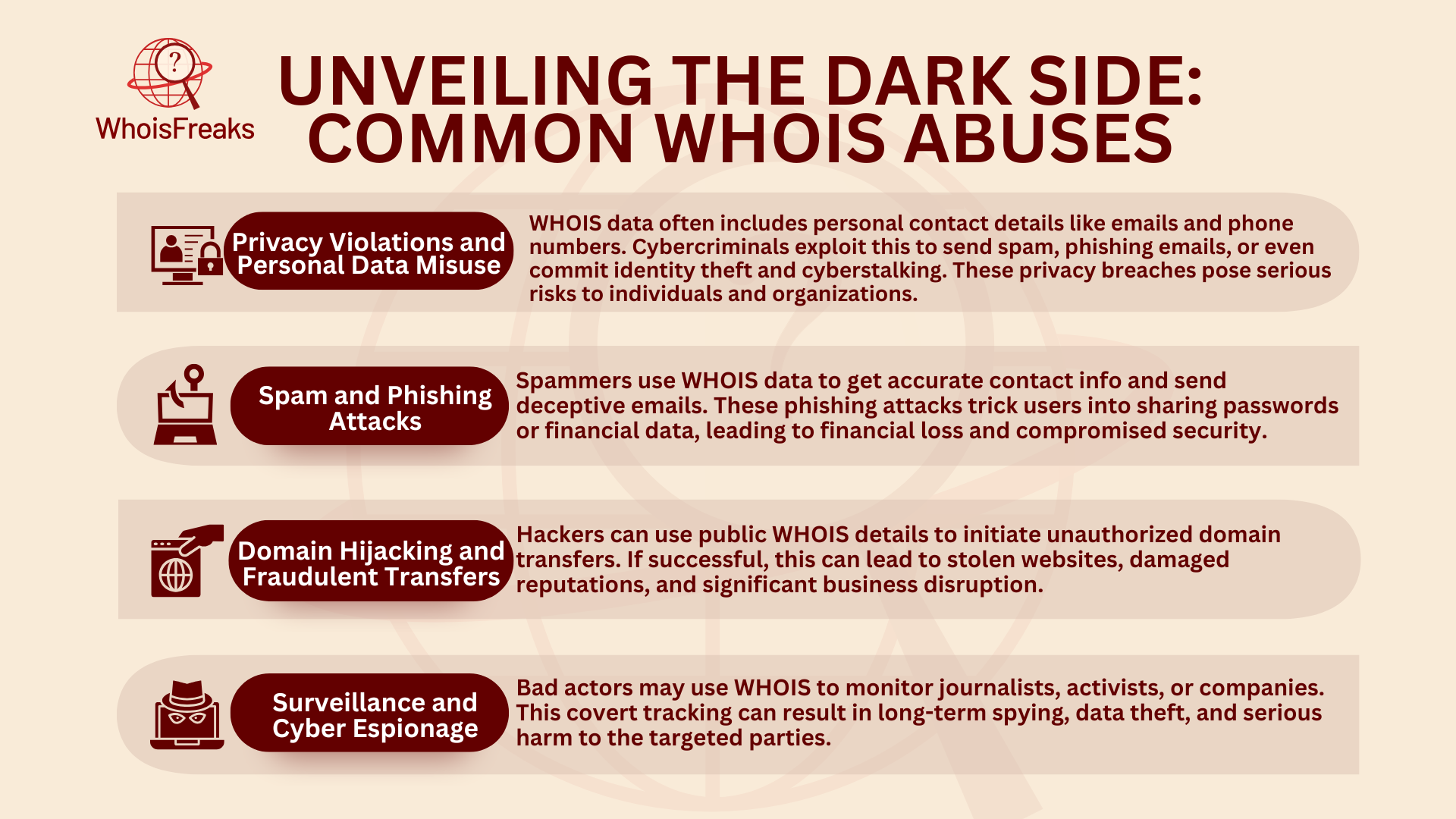
Bad actors often use WHOIS data to gather email addresses, phone numbers, and home addresses. This leads to lots of spam, tricky phishing emails, and unwanted messages. Even worse, WHOIS data has been used for ID theft, doxxing, and cyberstalking, which can bring big risks to people and groups.
Spammers and scammers misuse WHOIS databases to get accurate contact information and send phishing emails that fool people into giving up private info like passwords or money details. This helps them send phishing emails that fool people into giving up private info like passwords or money details. Many phishing attacks using WHOIS data have caused big money losses and leaks of both personal and work data.
Cyber crooks use WHOIS details to try illegal domain moves or steal domains by using public contact and admin info. These acts can cause big business problems, hurt a company’s name, and lead to large money loss.
Activists, news reporters, and companies can be watched when bad actors use WHOIS data to follow their moves, track people, or start cyber spying. These attacks often stay hidden for a long time and can bring deep harm to the people or groups targeted.
Knowing about these common abuses is key to spotting weak points and setting up smart steps to help stop them.
In response to growing concerns over privacy and data misuse, regulatory frameworks have significantly impacted WHOIS operations, creating new challenges for accessibility and transparency.
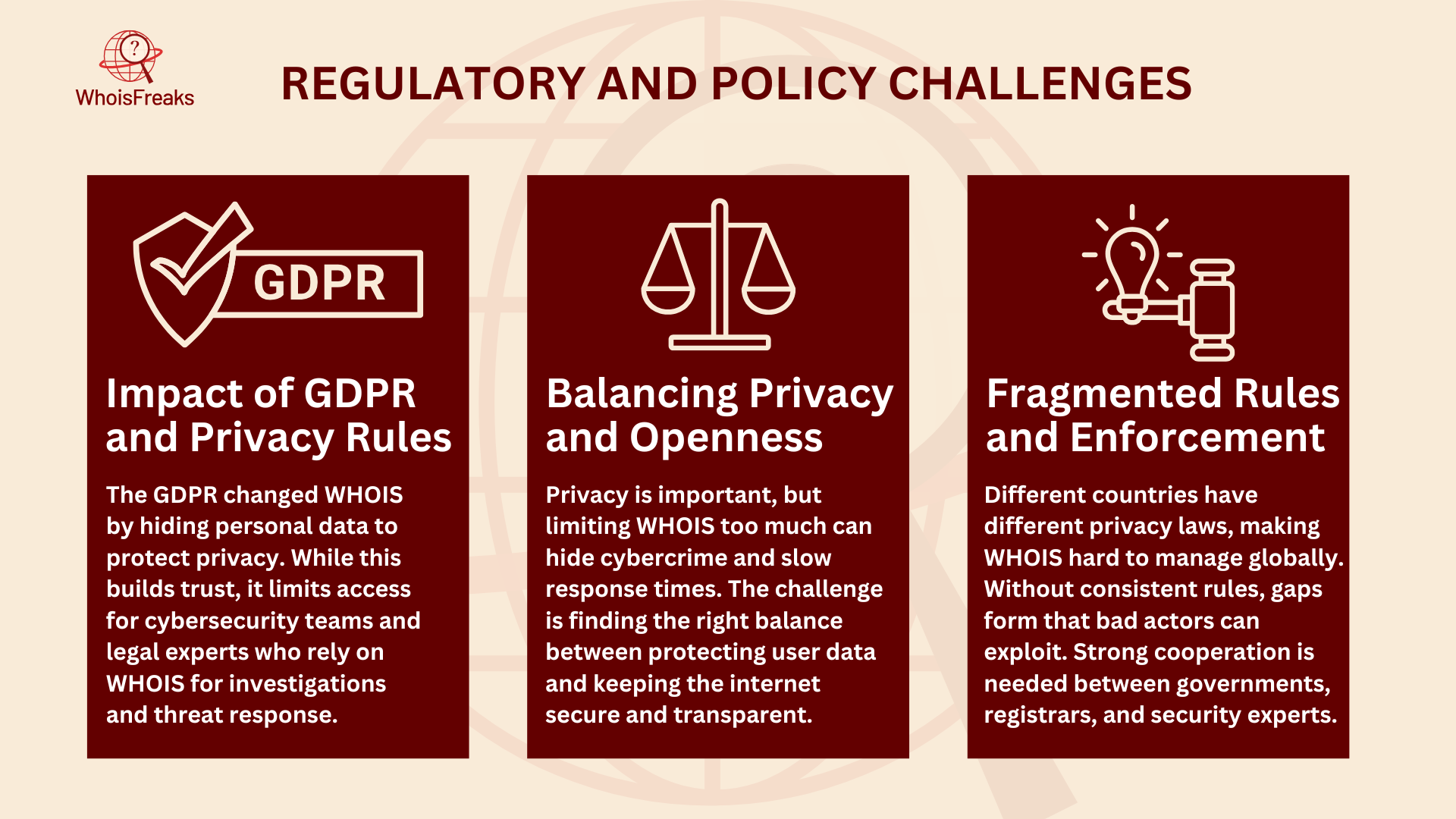
As worries grow about privacy and data misuse, new rules have changed how WHOIS works, bringing both challenges and chances to improve. The General Data Protection Regulation (GDPR), made by the European Union, marked a big shift for WHOIS. GDPR puts user privacy first by limiting public access to personal info. Because of this, WHOIS lists now often show only limited or hidden details. This can make it hard for cybersecurity experts, law groups, and intellectual property rights owners to do their work. Even with these bumps, GDPR’s strong push for better data safety has helped build trust and protect user rights in the online world.
Privacy rules like GDPR are key to keeping personal info safe. But they also bring a tough question: how do we keep privacy safe while also making sure there’s enough openness and security? This is the heart of the talk around WHOIS today. While it’s very important to protect privacy, cutting off too much access can help cybercriminals hide or make it harder for groups to solve issues fast. Finding a way to meet both privacy and openness needs is still one of the biggest tasks for the online world.
A major challenge in the WHOIS world is the mix of rules across different places. Not all countries have the same privacy laws, and this makes it tricky to follow WHOIS rules worldwide. Without clear and shared rules across countries, this patchwork creates gaps that bad actors can use. Fixing these rule and policy challenges needs teamwork between rule makers, registrars, privacy groups, and cybersecurity pros. Working together, they can build strong and flexible rules that protect privacy while still keeping the openness needed for a safe and trusted internet.
Prevention operates on two distinct planes: protecting your own domain registration data from being abused, and using WHOIS data defensibly to catch abuse directed at you or your organization.
ICANN-accredited registrars offer WHOIS privacy (sometimes called proxy or privacy protection) as an add-on or included service. These services replace your personal contact details in the public WHOIS record with the registrar's proxy contact information, while forwarding legitimate communications to you. The tradeoff is reduced discoverability for legitimate inquiries. Privacy services are appropriate for individual registrants; for organizations whose domains need to be publicly attributable for compliance or brand reasons, partial redaction (removing personal contact fields while retaining organizational identity) is a better fit.
Registry-level locks, sometimes called Registrar Lock or EPP status code clientTransferProhibited, prevent unauthorized domain transfers without explicit action by the registrant at the registrar level. Transfer Lock (clientUpdateProhibited) adds a further barrier against unauthorized DNS changes. Organizations that have experienced domain hijacking attempts should also consider registry-level locking through the Registrar Lock service offered by some registries for premium TLDs.
Most successful domain hijacking attempts begin with compromised registrar credentials. Two-factor authentication (2FA) using an authenticator app (not SMS, which is vulnerable to SIM-swapping) closes the primary attack vector. Enable 2FA on every registrar account, including ones managing secondary or defensive registrations.
DMARC, SPF, and DKIM protect your domain from being impersonated in email-based abuse. A DMARC record set to p=reject prevents attackers from successfully sending email that appears to come from your domain. SPF restricts which mail servers are authorized to send on your domain's behalf. DKIM adds a cryptographic signature that receiving mail servers can verify. All three records are added at the DNS level and cost nothing beyond configuration time.
DNS Security Extensions (DNSSEC) add a chain of cryptographic signatures to DNS responses, preventing cache poisoning and spoofing attacks that could redirect users from your legitimate domain to attacker-controlled infrastructure. Enabling DNSSEC requires both the registrar and the DNS hosting provider to support it.

Organizations face a different challenge: detecting when attackers register lookalike domains, clone your WHOIS registrant data, or hijack your subdomains. Continuous monitoring of WHOIS data for newly registered domains matching your brand, trademark, or registrant identifiers is the most effective early warning mechanism available. The WhoisFreaks Brand Monitoring product issues real-time alerts when new domains match patterns you define, including registrant email, organization name, or keyword matches in the domain string itself.
As WHOIS-related abuse continues to evolve, technological innovations have become pivotal in enhancing the security and privacy of domain registration information. Below are several key technologies and advancements contributing to safer WHOIS data management and data points:
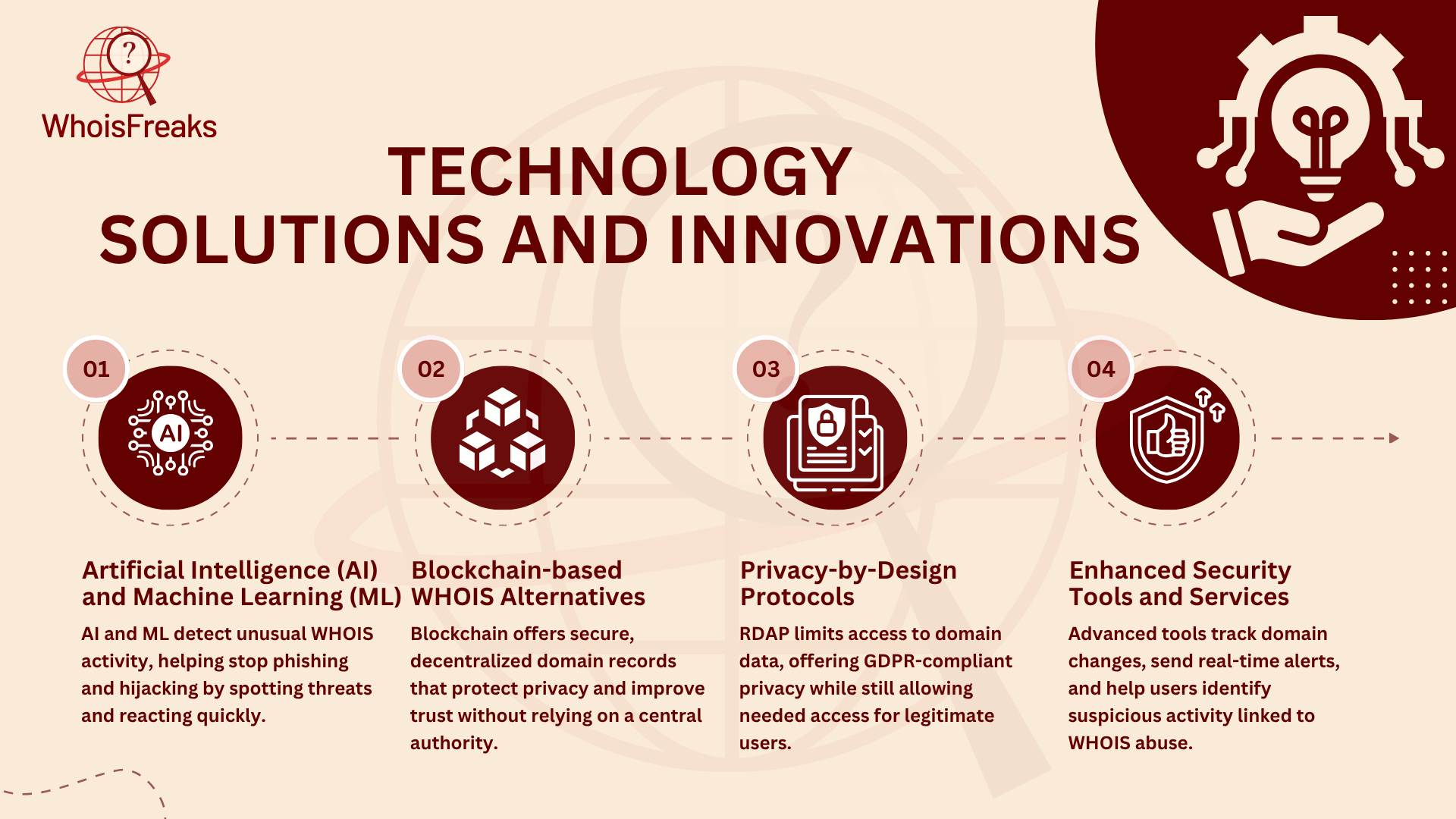
As WHOIS abuse keeps changing, new tech tools are playing a big role in keeping domain data safe and private. AI tools can check WHOIS search patterns to quickly spot shady actions and flag them for a closer look. Machine learning is great at finding odd signs that can point to phishing, domain hijacking, or other online threats. This helps experts act fast before things get worse.
New blockchain tools are bringing in a fresh way to handle domains, using a system that does not rely on one main database. With blockchain’s clear and unchangeable records, people can check domain details without hurting privacy. This could change how we manage domains within the domain name system, making the process safer and more private.
New privacy tools like RDAP (Registration Data Access Protocol) offer better safety than old WHOIS systems by showing data only when it’s really needed. RDAP has built-in ways to follow rules like GDPR, giving focused and limited access instead of showing all the data to the public.
Today’s domain protection tools offer strong tracking, instant alerts, and smart threat checks to stop unwanted domain changes. These tools help groups keep control over their online names and sites. Also, browser add-ons and security apps help everyday users by warning them about risky domain names or shady actions tied to WHOIS misuse.
For teams building automated abuse detection pipelines, programmatic WHOIS access via the WhoisFreaks WHOIS API provides structured JSON responses with coverage across more than 2,000 TLDs.
To illustrate the tangible risks associated with WHOIS data misuse, let's examine several documented cases:
In September 2021, the domain registrar Epik suffered a significant data breach. Hackers, identifying themselves as part of the Anonymous collective, accessed and released over 180 gigabytes of data (Source: Wired, September 2021). This included personal information of customers, domain history, purchase records, and details from Epik's WHOIS privacy service. The breach exposed approximately 15 million unique email addresses, encompassing both customers and non-customers whose information had been scraped from WHOIS records (as reported by DDoSecrets and covered by Wired, September 2021).The incident underscored the vulnerabilities inherent in storing and managing WHOIS data, especially when privacy services are compromised.
In a landmark legal case, Register.com sued Verio Inc. for harvesting data from its WHOIS database to conduct unsolicited marketing campaigns. Verio used automated tools to collect newly registered domain information and subsequently contacted these registrants with promotional offers. The court ruled in favor of Register.com, emphasizing that Verio's actions violated the terms of use associated with the WHOIS data. This case highlighted the potential for WHOIS data to be exploited for commercial gain and set a precedent for how such data should be ethically and legally handled.
An ICANN-commissioned study on WHOIS privacy and proxy service abuse found that a significant percentage of domains associated with malicious activities utilized WHOIS privacy or proxy services to conceal registrant identities. Specifically, 46% of sampled advanced fee fraud cases involved domains registered through such services. This obfuscation hampers efforts by law enforcement and cybersecurity professionals to trace and mitigate fraudulent activities, demonstrating how privacy tools, while beneficial for legitimate users, can also shield malicious actors.
For teams using WHOIS data in active investigations, WHOIS history in incident response covers chain-of-custody documentation and how historical records support legal proceedings.

WHOIS records contain several fields that, individually, may appear normal, but in combination signal high abuse probability. Security teams performing triage on suspicious domains should examine these five indicators.
Domains registered within the last 30 days account for a disproportionate share of phishing infrastructure. A domain less than 30 days old sending email or hosting a login form is a high-priority investigation target regardless of other factors.
Certain registrars have documented histories of slow or non-existent abuse response. When a suspicious domain is registered through a registrar with a low response rate in ICANN's DAAR (Domain Abuse Activity Reporting) dataset, that alone elevates the risk score.
WHOIS privacy services are legitimate for most registrants. However, domains in abuse-prone TLDs such as .xyz, .top, .tk, and .club, combined with full WHOIS redaction, represent a pattern consistent with registration-scale phishing or spam operations. The 2013 ICANN study confirmed that 46% of advanced fee fraud domains in the sample used privacy or proxy services.
When a bulk WHOIS query across a set of suspicious domains returns identical or near-identical registrant email addresses, organization names, or phone numbers, this indicates a shared registration infrastructure. Registrant clustering is one of the most reliable indicators of coordinated abuse campaigns.
A domain without clientTransferProhibited or clientUpdateProhibited status is more vulnerable to unauthorized transfer. Domains actively used for malicious purposes are often kept deliberately unlocked so the operator can abandon and re-register if the domain is blocked.
Monitoring newly registered domains in bulk is one of the most scalable early-warning approaches for phishing infrastructure detection.
In analysis of phishing-infrastructure domains submitted to WhoisFreaks threat research queries, a consistent pattern emerges: domains exhibiting three or more of the five indicators above account for the majority of confirmed abuse cases in the submitted sets. Single-indicator hits generate significant false positives; multi-indicator correlation is where WHOIS-based detection earns its operational value.
WhoisFreaks' Reverse WHOIS API lets analysts run bulk queries across these five indicators at scale, returning all domains associated with a given registrant email, organization name, or phone number. This is particularly useful for identifying infrastructure clusters before a campaign fully deploys.
Reporting domain abuse involves three parties: the registrar (who controls whether the domain stays registered), the registry (who controls the TLD), and coordinating organizations like ICANN. The correct channel depends on the abuse type.
Run a WHOIS lookup on the suspicious domain. The "Registrar Abuse Contact Email" field is present in WHOIS records for ICANN-accredited registrars and is the primary reporting destination. Most registrars require you to email this address directly with the domain name, abuse type, evidence (screenshots, email headers, archived URLs), and a description of the harm.
| Abuse Type | Primary Reporting Channel | Secondary Channel |
|---|---|---|
| Phishing | Registrar abuse contact | Google Safe Browsing (safebrowsing.google.com/safebrowsing/report_phish/) |
| Malware | Registrar abuse contact | abuse.ch (urlhaus.abuse.ch) |
| Spam | Registrar abuse contact | Spamhaus (spamhaus.org/submit) |
| Domain hijacking | Registrar abuse contact | ICANN Compliance (icann.org/compliance/complaint) |
| Trademark infringement | UDRP filing via WIPO or NAF | ICANN Contractual Compliance |
| Persistent registrar non-response | ICANN Contractual Compliance | Relevant ccTLD registry |
Registrars act faster when reports include the exact domain URL, archived evidence (archive.org or a local screenshot with timestamp), email headers if the abuse arrived via email, and a clear statement of the harm. Vague reports frequently result in no action.
ICANN requires registrars to acknowledge abuse reports. If you receive no acknowledgment, file complaint at ICANN Contractual Compliance. Include the date you first reported to the registrar and any reference number they provided.
WHOIS plays a big part in keeping the internet clear and fair by sharing key details about who owns a domain and who to reach for tech help. This openness brings many good things, but it also brings some risks. Bad actors can misuse WHOIS data for spam, phishing, ID theft, or domain hijacking, turning this helpful tool into a possible threat for both domain owners and companies. The big challenge is finding the right mix between staying open and keeping privacy safe, while also addressing any potential security gaps.
To face these challenges, we need to take a mix of smart steps. On the user and business side, using WHOIS privacy services, setting up strong account security, and staying sharp to spot threats can lower the risk of abuse. On the policy side, leaders must keep making privacy rules like GDPR better, so they protect people without stopping the work of security teams, law groups, and rights holders who need WHOIS data. New tech, like AI tools, blockchain systems, and anti-spam technologies, can also help make WHOIS systems stronger and more trustworthy. Organizations defending against lookalike domains and brand impersonation can combine WHOIS abuse detection with brand monitoring to cover both the registration event and the active use of the domain.
Keeping WHOIS data safe takes teamwork. Domain owners, registrars, rule makers, cybersecurity pros, and even everyday users all have a part to play in using WHOIS the right way and asking for smart changes. By working together, we can make sure WHOIS keeps doing what it was made to do build trust and fairness online while cutting down on the risks of misuse.

Pull WHOIS, live DNS, and subdomains from WhoisFreaks in XSOAR. Score the domain before any block fires. Auto-block high-risk or route to analyst review.
12 min read

ExpiredDomains.net does not offer any API to integrate its services into customer infrastructure. To access expired or deleted domain names via an API, you would need to rely on scraping or third‑party providers.
9 min read

WhoisFreaks offers daily & historical domain data with WHOIS/DNS insights for threat analysis.
9 min read