
Blog
DNS Server Purpose: What It Does and How It Works
Written By Qasim, WhoisFreaks Team Published: October 24, 2025, Last Updated: April 14, 2026

Blog
Written By Qasim, WhoisFreaks Team Published: October 24, 2025, Last Updated: April 14, 2026
A DNS server translates human-readable domain names into the numeric IP addresses that computers use to communicate. Every time you type a URL into a browser, a DNS server is working in the background to find the right address and return it to your device, typically in under 100 milliseconds.
Without DNS, navigating the internet would require memorizing strings of numbers. The IP address for google.com is 142.250.217.46. DNS makes that number invisible to the user while making it accessible to the machine.
This guide covers how DNS servers work, the four server types involved in every resolution, the record types DNS manages, how DNS affects speed and reliability, and where DNS fits into network security.
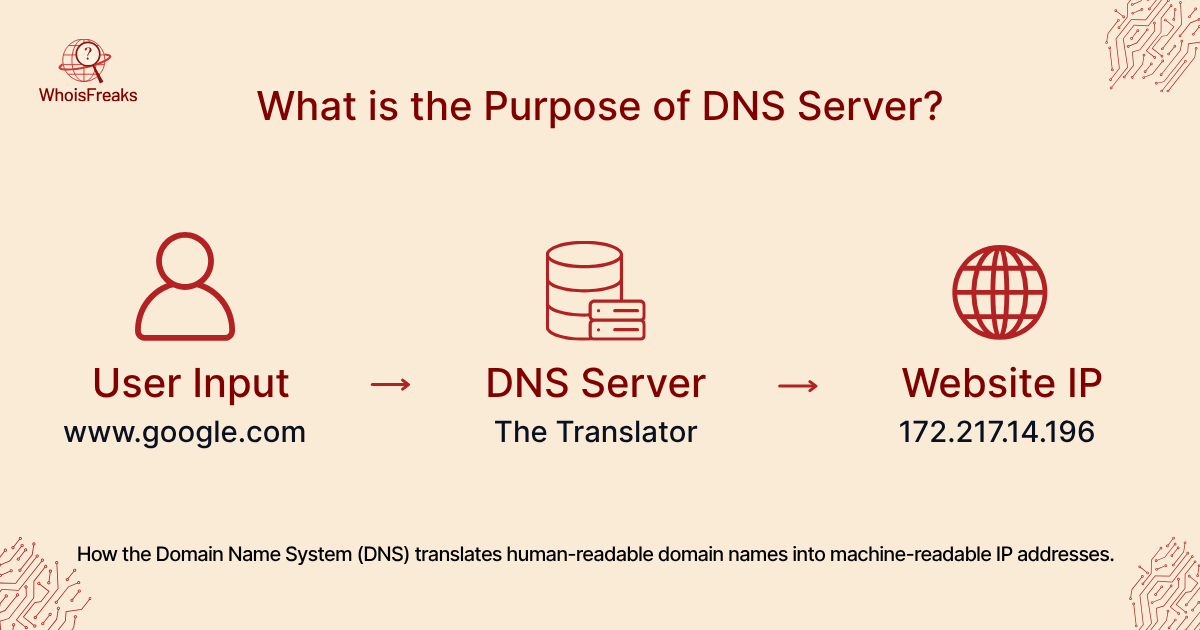
A DNS server is a computer that translates domain names into IP addresses. When you type a domain name into a browser, your device cannot connect to it directly because computers communicate using numbers, not names. The DNS server bridges that gap, looking up the IP address that corresponds to the name you entered and returning it so your browser can establish the connection.
DNS stands for Domain Name System. The system is hierarchical and distributed, meaning no single server handles all queries. Four distinct server types work together to complete every resolution: recursive resolvers, root nameservers, TLD nameservers, and authoritative nameservers. Each handles a specific step in the lookup chain.
Without DNS servers, every user would need to memorize the numeric IP address of every website they visit. The address for google.com is 142.250.217.46. DNS makes that number irrelevant by letting you type the name instead.
Behind the scenes, resolving a domain name involves multiple steps and servers in a hierarchy, including an authoritative nameserver. A typical DNS lookup process works like this:
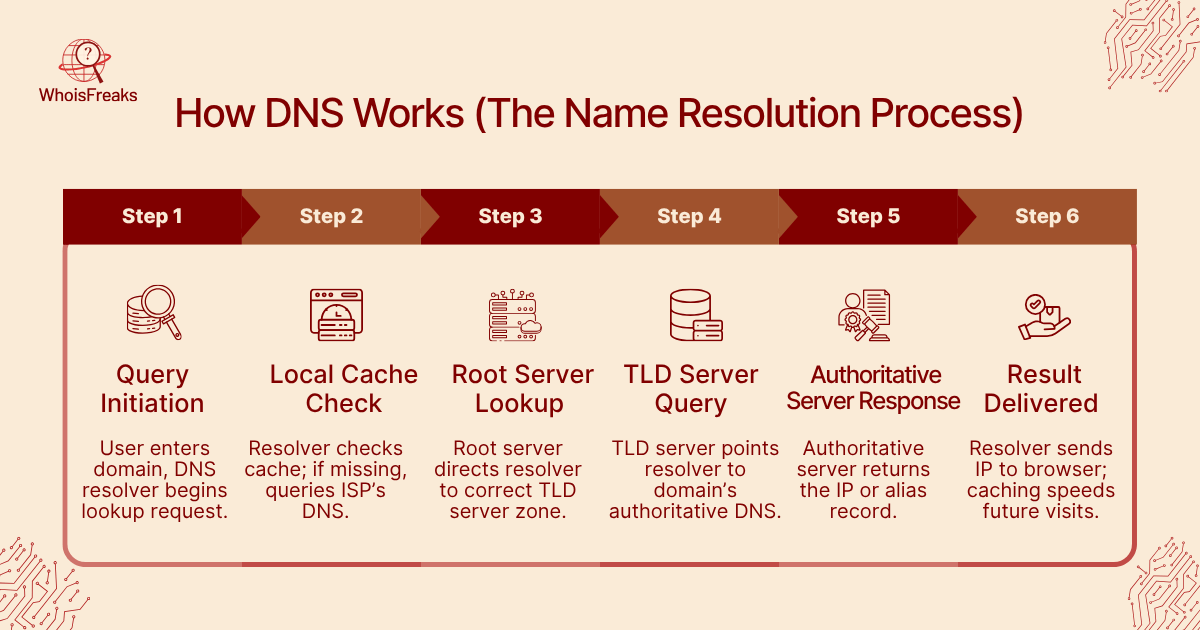
When you enter a domain (e.g.www.screenshotapi.net) in your browser, the computer’s DNS resolver starts the request.
The resolver first checks its own cache (memory) to see if the IP is already known. If it finds the record, it returns the IP immediately. Otherwise, it asks a higher-level server (often your Internet Service Provider’s DNS).
If the ISP’s resolver doesn’t have the answer cached, it queries one of the root name servers. A root server knows where to find the Top-Level Domain (TLD) servers (for .com, .net, etc.) and directs the query accordingly.
The resolver then contacts the TLD name server (for example, the .com server) which points to the authoritative name server for the specific domain.
Finally, the resolver asks the authoritative DNS server of the domain to obtain the IP address. The authoritative server contains the DNS information of that domain and responds with the A (or AAAA) record containing the IP. In case the record is an alias (CNAME), then the resolver goes with it until it gets an IP.
The resolver passes the IP address back to your computer, and your browser connects to that IP to load the website.
This multi-step process happens in milliseconds. Along the way, DNS caching plays a key role: each resolver (your computer, your ISP) keeps recently requested records for a while. This means that repeat visits are faster and put less load on the DNS system, thanks to recursive DNS servers.
TTL stands for Time to Live. Every DNS record carries a TTL value measured in seconds. This number tells resolvers how long to cache the record before discarding it and fetching a fresh copy.
A TTL of 3600 means the resolver caches the record for one hour. A TTL of 86400 means one day. During that window, repeat queries for the same domain skip the full resolution chain and return the cached answer immediately. This is why DNS is fast for popular domains visited frequently.
TTL directly affects how quickly DNS changes propagate across the internet. Lowering a domain's TTL to 300 seconds (5 minutes) before a planned server migration ensures most resolvers pick up the new IP address within minutes. Leaving TTL at 86400 means some users may receive the old IP address for up to 24 hours after the migration.
Four distinct server types handle every DNS resolution. Understanding their roles clarifies why DNS queries involve multiple network hops before your browser receives an IP address.
Recursive Resolver
The recursive resolver is the first server your device contacts. It acts as an intermediary, doing the work of querying other servers on your behalf. Your internet service provider typically operates the recursive resolver you use by default, though public options such as Google's 8.8.8.8 or Cloudflare's 1.1.1.1 are available to anyone. When the resolver has a recent answer cached, it returns the IP address immediately without contacting any other servers.
Root Nameserver
If the recursive resolver has no cached answer, it queries one of the 13 root nameserver authorities. Root nameservers do not know the IP address for any specific domain. Their job is narrower: they know which TLD nameserver is responsible for a given top-level domain and direct the resolver there. There are 13 root nameserver identities, labeled A through M, though each is backed by hundreds of physical servers distributed globally via Anycast routing.
TLD Nameserver
The TLD (top-level domain) nameserver handles the final segment of a domain name. The .com TLD server handles all .com domains. The .org TLD server handles all .org domains. When the recursive resolver contacts the TLD nameserver, it receives the address of the authoritative nameserver for the specific domain it is looking for.
Authoritative Nameserver
The authoritative nameserver holds the actual DNS records for a domain. It is the final stop in the resolution chain and the source of truth. When the recursive resolver queries the authoritative nameserver for example.com, it returns the A record containing the IP address, or a CNAME record pointing to another hostname. The domain owner controls what the authoritative nameserver returns. Changing a server, migrating a website, or redirecting email all happen by updating records on the authoritative nameserver.
Every DNS zone contains resource records. Each record type serves a specific purpose in routing traffic, verifying identity, or delegating authority.
| Record Type | Full Name | Purpose |
|---|---|---|
| A | Address | Maps a hostname to an IPv4 address |
| AAAA | IPv6 Address | Maps a hostname to an IPv6 address |
| CNAME | Canonical Name | Creates an alias pointing one hostname to another |
| MX | Mail Exchange | Specifies which server handles email for the domain |
| NS | Name Server | Identifies the authoritative nameservers for the domain |
| TXT | Text | Stores arbitrary text, used for SPF, DKIM, and domain verification |
| SOA | Start of Authority | Contains zone metadata: primary nameserver, admin contact, serial number, TTL timers |
| PTR | Pointer | Maps an IP address back to a hostname (reverse DNS) |
| SPF | Sender Policy Framework | Authorizes which servers may send email on behalf of the domain (stored as a TXT record) |
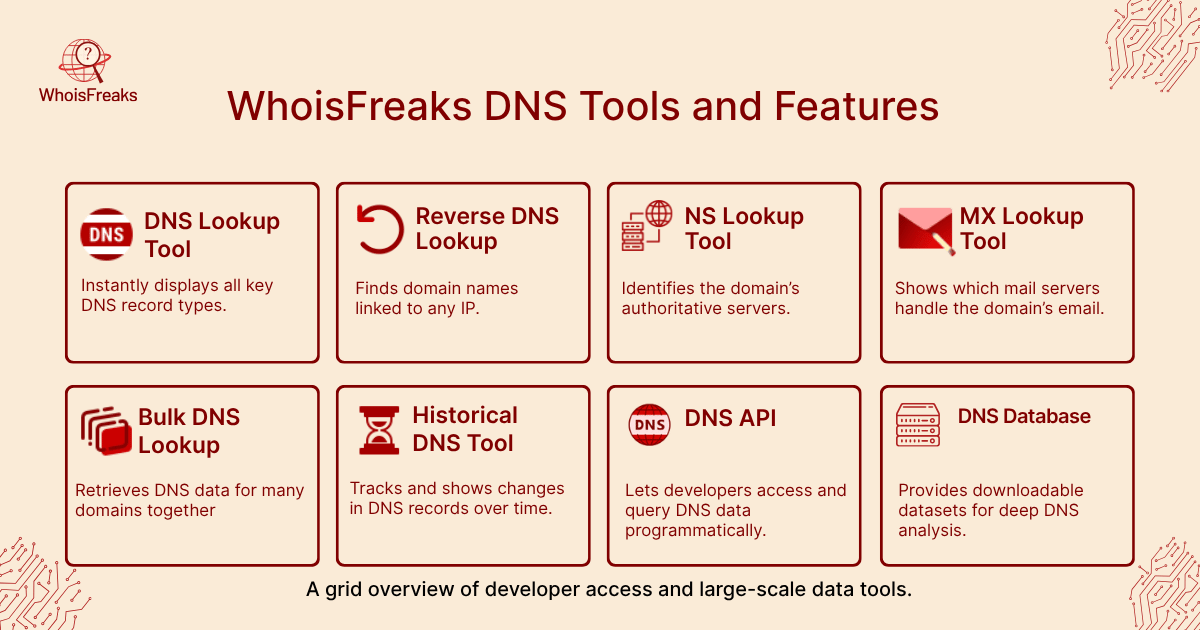
Security teams query these records routinely. An MX record change can indicate a domain has been compromised or is being used for phishing. A new NS record may signal a hostile nameserver takeover. WhoisFreaks stores historical DNS records across all major record types, making it possible to detect these changes after the fact. The Historical DNS Lookup tool surfaces record changes with timestamps, covering A, AAAA, MX, NS, and TXT history.
DNS brings many important benefits to Internet users and networks, such as ensuring the correct IP address is found for each domain. Key advantages include:
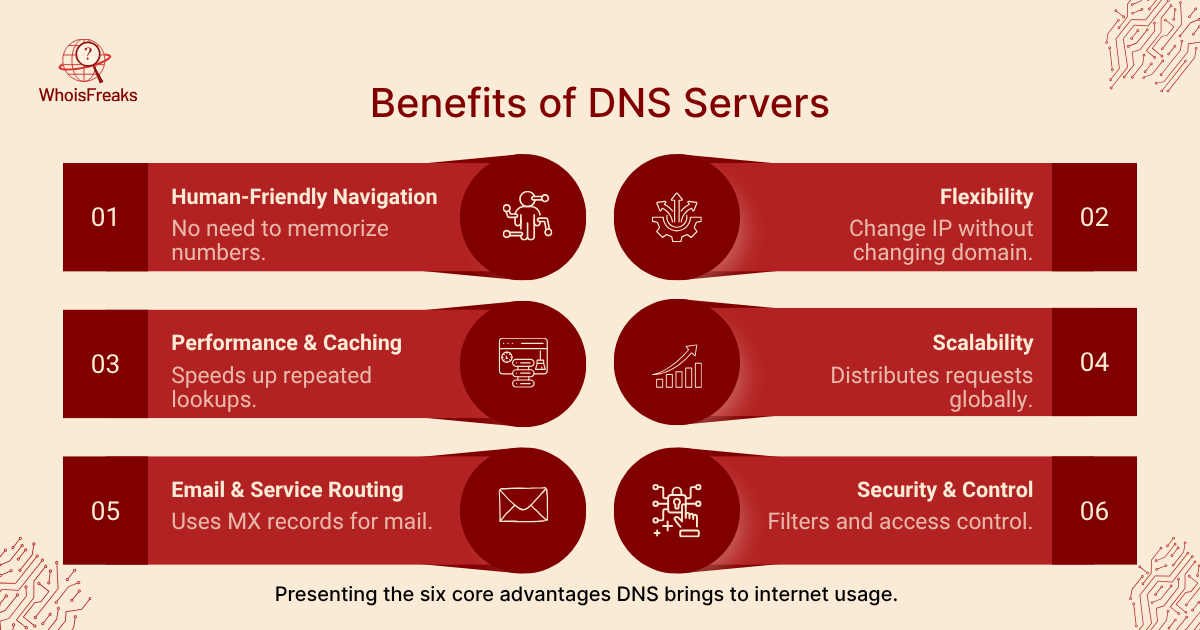
In summary, DNS makes the Internet user-friendly, flexible, and robust. It hides the complexity of numerical addressing from users, allows networks to scale and adapt, and supports faster, more reliable connections.
DNS is critical infrastructure, which makes it a target. Because the original DNS protocol was designed for reliability rather than security, it carries inherent vulnerabilities that attackers continue to exploit.
DNS Cache Poisoning
A DNS cache poisoning attack injects false records into a resolver's cache. If successful, the resolver serves a malicious IP address to every user who queries the affected domain until the cache expires. The user's browser connects to an attacker-controlled server while the address bar shows the legitimate domain name. This technique underlies many credential-harvesting and malware delivery campaigns.
DNS Hijacking
DNS hijacking modifies the DNS records at the authoritative nameserver level, typically by compromising the domain registrar account or the nameserver credentials. Once the attacker controls the NS or A records, all traffic for the domain routes through their infrastructure. Unlike cache poisoning, hijacking affects every user globally and persists until the legitimate owner regains control.
DNSSEC
DNSSEC (Domain Name System Security Extensions) adds cryptographic signatures to DNS records. A validating resolver can verify that the records it receives have not been tampered with in transit. DNSSEC does not encrypt queries, but it does detect tampering. As of 2024, DNSSEC adoption across .com domains remains under 5%, leaving the majority of the internet's domains without this protection layer.
DNS as a Security Signal
Security teams use DNS data offensively as well as defensively. Querying historical DNS records for a suspicious domain reveals infrastructure pivots: when a malicious actor moved the domain to a new IP, which registrar was used, and whether the domain shared hosting with other known-bad infrastructure. The WhoisFreaks Historical DNS Lookup tool surfaces these record changes with timestamps across A, AAAA, MX, NS, and TXT history.
WhoisFreaks provides a set of DNS tools for analysts, developers, and IT teams who need to inspect live or historical DNS records at scale. The DNS Lookup tool returns all eight major record types for any domain instantly. For investigations that require historical context, the Historical DNS Lookup tool covers record changes over time across A, AAAA, MX, NS, and TXT records, drawing on a database of over 14 billion DNS records.
Developers who need programmatic access to DNS data can use the WhoisFreaks DNS API to query A, MX, NS, and other record types at scale. Full API documentation and database download options are available at whoisfreaks.com.
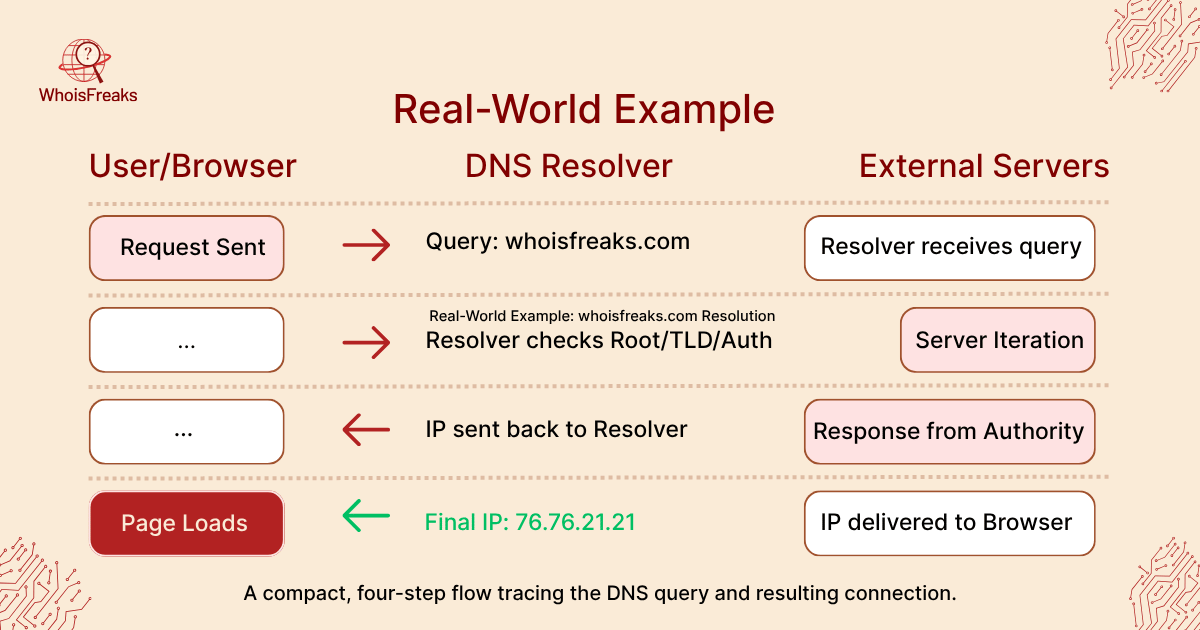
Consider what happens when you visit a website like www.whoisfreaks.com. Your computer asks a DNS resolver for www.whoisfreaks.com. Through the steps above, it eventually finds the IP address (say 76.76.21.21) where the site is hosted. The web browser then connects to that IP. All of this from typing the name to seeing the site relies entirely on DNS, which also needs to be safeguarded against DNS attacks.
As another example, large companies often have public DNS servers to offer faster lookups. Google’s DNS (8.8.8.8) can resolve any public domain, including queries that reach the TLD nameserver and it helps many users get fast, reliable name resolution. Cloudflare’s 1.1.1.1 is another popular public DNS focused on speed and privacy. On the other hand, a corporate network might run its own DNS servers internally to resolve employee laptops or IoT devices. These private DNS servers are isolated from the Internet at large, which provides greater control and security over company resources.
Everyday scenarios rely on DNS: clicking an email link, accessing a cloud service, or even loading ads involves DNS lookups. Email delivery uses DNS (MX records) so your mail server knows where to send messages. Content Delivery Networks use DNS to send you to the nearest server. Network tools and security systems use DNS data to filter malicious domains. Even logging into apps or games often requires DNS resolution. In short, DNS is quietly enabling nearly every Internet-based activity by utilizing various resource records .
DNS is the infrastructure layer that makes named internet resources accessible. Every browser request, every email delivery, every API call to a cloud service starts with a DNS query. The four-server resolution chain completes that query in milliseconds, and caching keeps the system fast under massive load.
For security teams, DNS is also a data layer. Record changes, infrastructure pivots, and malicious domain registrations all leave traces in DNS history. Analyzing those traces is a core part of incident response, phishing investigation, and brand protection work.
If you need to inspect DNS records live or investigate historical configurations, the WhoisFreaks DNS Lookup and Historical DNS tools are available free at whoisfreaks.com.

Discover essential insights on DNS poisoning and learn practical steps to safeguard your online presence. Read the article for vital protection tips.
9 min read

Learn how a DNS flooder can threaten your network security and discover practical measures to protect your systems. Read more to safeguard your network.
9 min read