
Guide
The Comprehensive History of DNS: Key Milestones and Developments
Written By Qasim, WhoisFreaks Team Published: December 02, 2025, Last Updated: December 10, 2025

Guide
Written By Qasim, WhoisFreaks Team Published: December 02, 2025, Last Updated: December 10, 2025
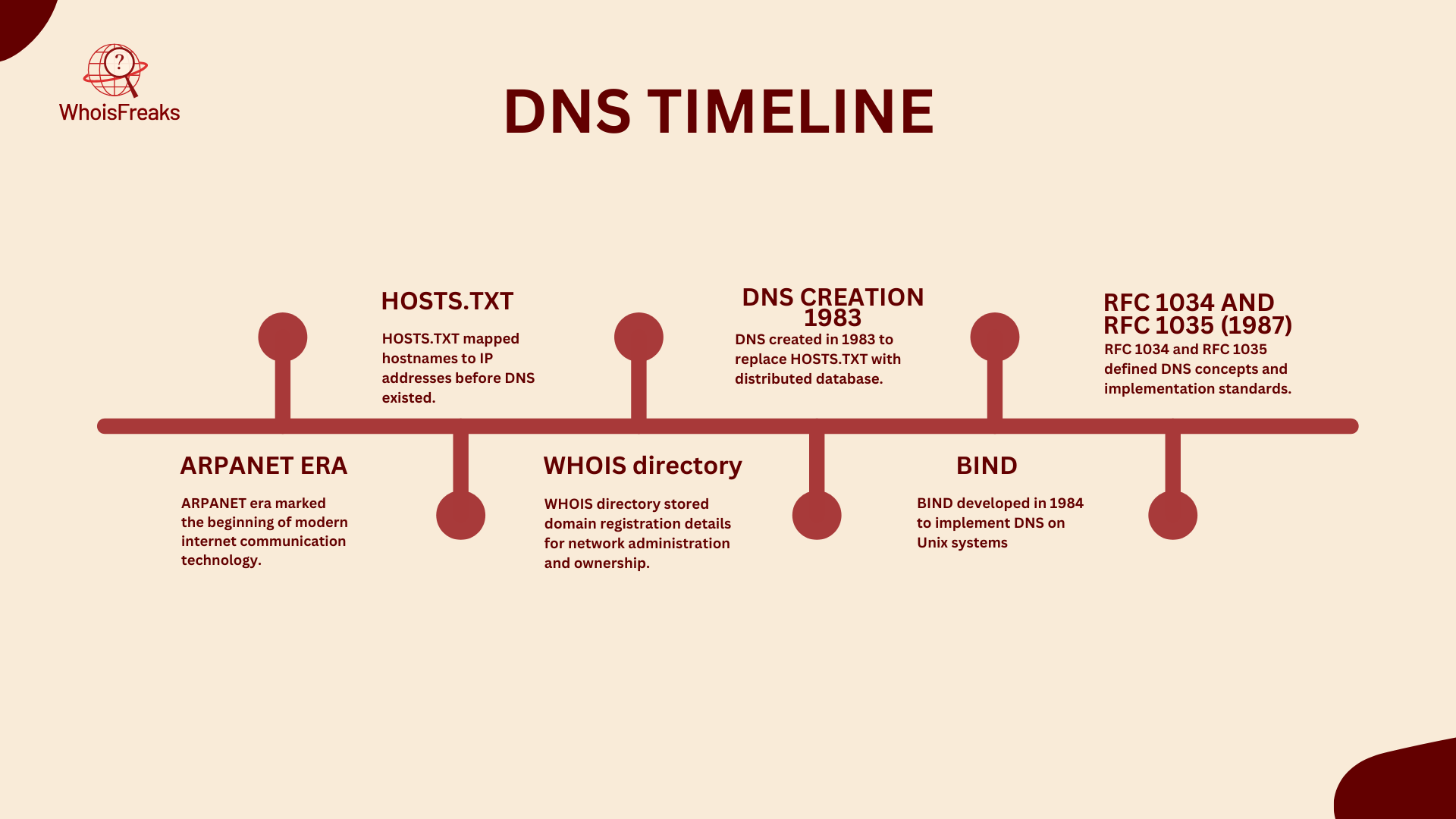
As the ARPANet expanded, ARPANet directory was created to contains ARPANet users, hosts and contact information. It was also called Whois directory.
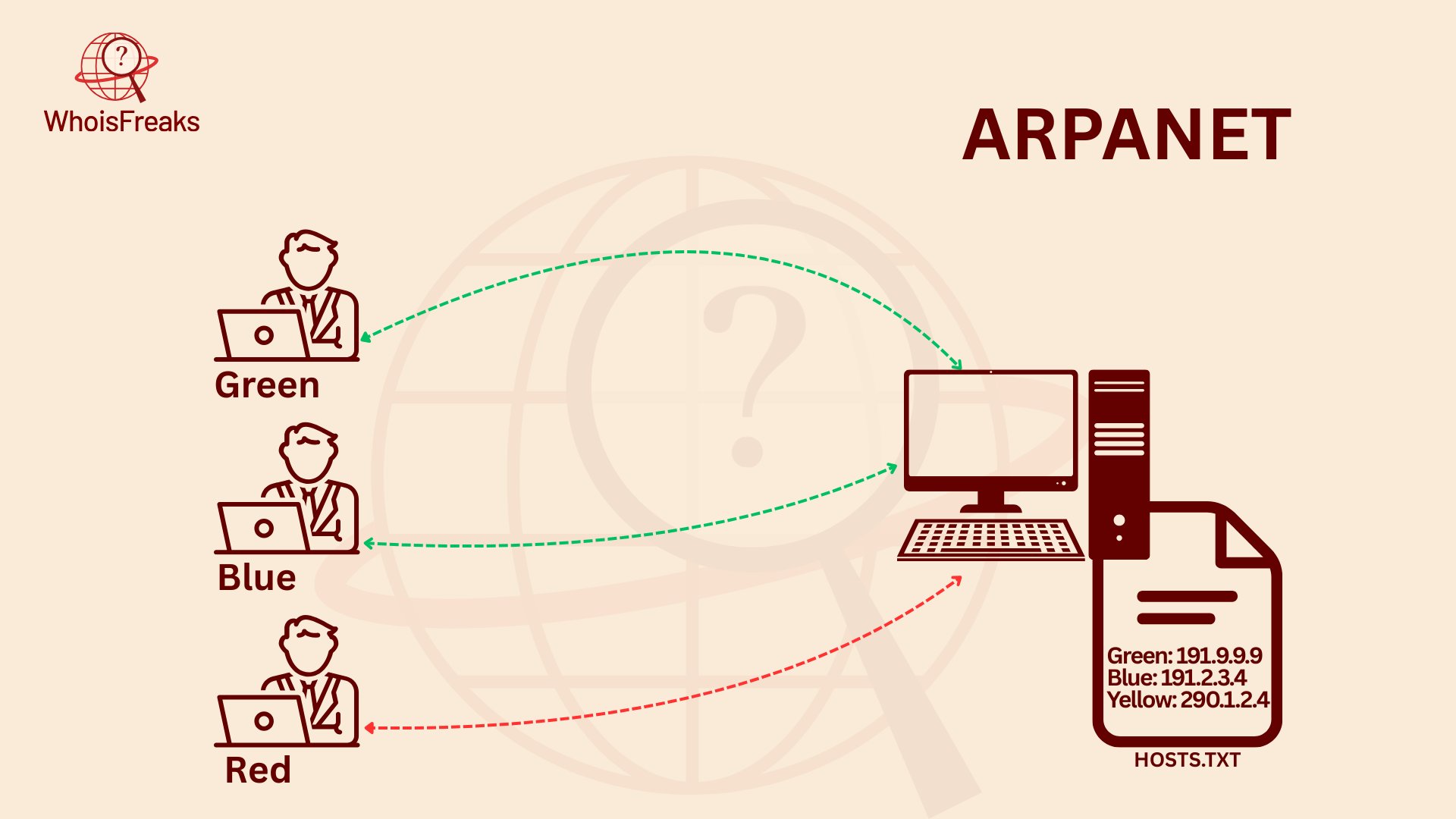
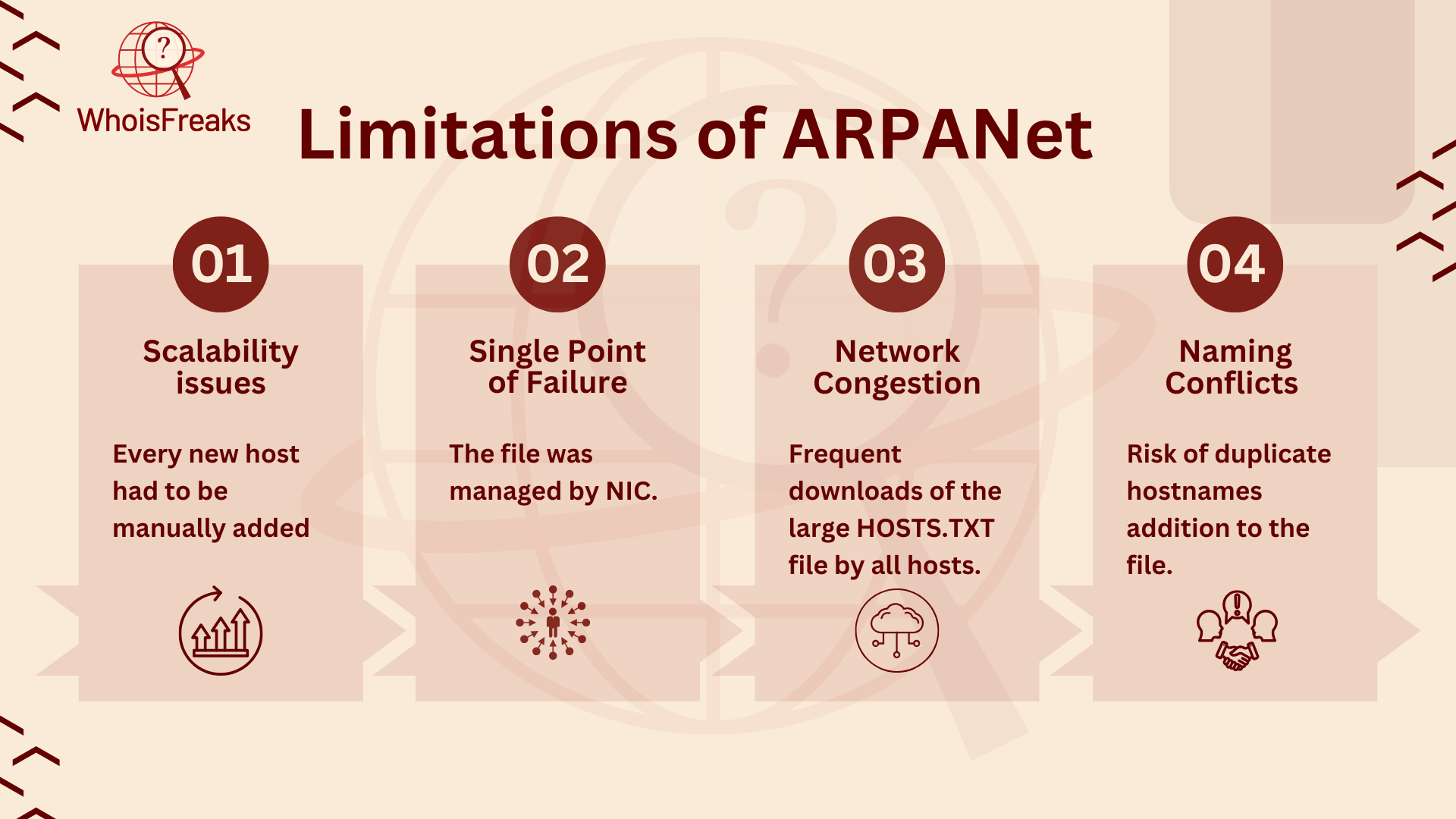
As the ARPANet expanded, managing the centralized HOSTS.TXT file became increasingly difficult. The growing size of the network introduced several limitations, which ultimately led to the creation of the Domain Name System (DNS). These limitations included:
The first six generic top-level domains (TLDs) were made available in 1984: .com, .edu, .gov, .mil, .net, and .org. These TLDs were introduced to provide a way to categorize domain names and make them easier to remember. The introduction of TLDs marked a significant milestone in the development of the DNS.
The initial implementation of the Domain Name System was named Jeeves. It was later followed by a more robust and widely adopted implementation called BIND (Berkeley Internet Name Domain), developed by students at UC Berkeley for use with Unix systems. BIND eventually became the de facto standard DNS server software on the internet. Internet systems consortium is the official maintainer of BIND software.
In 1985, DARPA (ARPA) pushed users to use DNS addresses instead of IP addresses. This marked a significant shift towards the widespread adoption of the DNS. The use of DNS addresses made it easier for users to access websites and online services.
In 1985, DNS management was assigned to SRI International (Stanford research institute). SRI was responsible for managing the DNS database and ensuring the smooth operation of the system. The assignment of DNS management to SRI marked a significant milestone in the development of the DNS.
In 1986, domain name registrations became publicly accessible, allowing anyone to register a domain through a domain name registry. This marked a major milestone in the evolution of DNS and the internet. The involvement of domain registries led to a rapid surge in the number of registered domain names.
Nowadays, domains are registered through accredited domain registrars, which act as intermediaries between the registrant (domain owner) and domain registries that manage specific top-level domains (TLDs).
Domain name system became foundational standard after the creation of Internet Engineering Task Force (IETF) in 1986.
In 1987, Paul Mockapetris published the comprehensive details of the Domain Name System (DNS) — from its conceptual framework to its practical implementation — in RFC 1034 and RFC 1035. It became one of the internet standards.
RFC 1034 and RFC 1035 define the foundation of the Domain Name System protocol. Covering everything from specifications and features to practical implementation, these RFCs hold significant importance in the development of the internet. They form the fundamental basis of DNS.
RFC 1034 defines the architecture of the DNS. It explains key concepts such as the domain name space, resource records, name servers, authoritative name servers, root servers, zones, and resolvers, and how they interact with each other.
In RFC 1034, a client interacts with a resolver, which then sends a request to a name server to obtain the corresponding IP address. Name servers either return the IP address directly or refer the resolver to another name server. This process is recursive, continuing through multiple name servers until the final result is obtained.
RFC 1035 provides the implementation details that support the architecture defined in RFC 1034. It outlines the operations and algorithms used to resolve domain names into IP addresses. The RFC also introduces caching mechanisms to improve performance and reduce the number of queries sent to root servers.It also introduces the zone transfers from one name server to another. Additionally, it specifies the format of DNS messages and defines various DNS record types, such as A records, MX records, and others.
DNS Queries are requests made by a client (like a browser) to a DNS server to resolve a domain name into an IP address or other DNS-related information. There are three main types of queries: recursive, iterative, and non-recursive.
Resource Records (RRs) are the data entries in the DNS system that provide information about domain names. Each record has a specific type (like A, AAAA, CNAME, MX, NS, TXT, etc.) and contains fields such as name, type, class, TTL (time to live), and data.
DNS queries are used to retrieve resource records, which are essential components of the DNS.
The DNS database is a distributed, hierarchical system that stores information about domain names, including their corresponding IP addresses and mail servers. It is structured like an inverted tree, with the root at the top, followed by top-level domains (TLDs), second-level domains, and subdomains branching out beneath.
DNS Protocol is an application-layer protocol used for querying and exchanging DNS information over IP networks. It typically runs over UDP (port 53) for queries, and TCP is used for larger responses (like zone transfers). The protocol defines message formats, query types, and response codes to enable communication between clients and DNS servers.
The DNS protocol defines the data structures and communication processes used for exchanging information within the DNS.
In 1995, the first version of the Secure Sockets Layer (SSL) protocol was released. SSL provided a way to encrypt data transmitted between a web browser and a web servers. SSL eventually evolved into TLS (Transport Layer Security), which is now the standard protocol for securing internet traffic.
In 2005, the Domain Name System Security Extensions (DNSSEC) were introduced to increase the security of the DNS. DNSSEC provided a way to authenticate the origin of DNS data and ensure its integrity.
DNSSEC adds a layer of security to DNS by ensuring that DNS responses are authentic and haven't been tampered with. It uses digital signatures and public key cryptography to verify the integrity of DNS data.
DNS over HTTPS (DoH) and DNS over TLS (DoT) both encrypt DNS queries to enhance privacy and security by preventing third parties from viewing or tampering with DNS traffic. DoH sends DNS queries over encrypted HTTPS on port 443, allowing it to blend in with regular web traffic and making it harder to block or monitor. DoT, on the other hand, uses TLS encryption over a dedicated port (usually 853), providing similar privacy benefits but making it easier to identify and potentially block. While both protocols protect DNS traffic, they mainly differ in how they operate and integrate within networks.